Android 4.4.3 KitKat Update: Leaked Change Log Follows Several Newly Discovered Build Numbers

Murmurs of there being a new Android update on the way have culminated with change log information for the upcoming update being leaked.
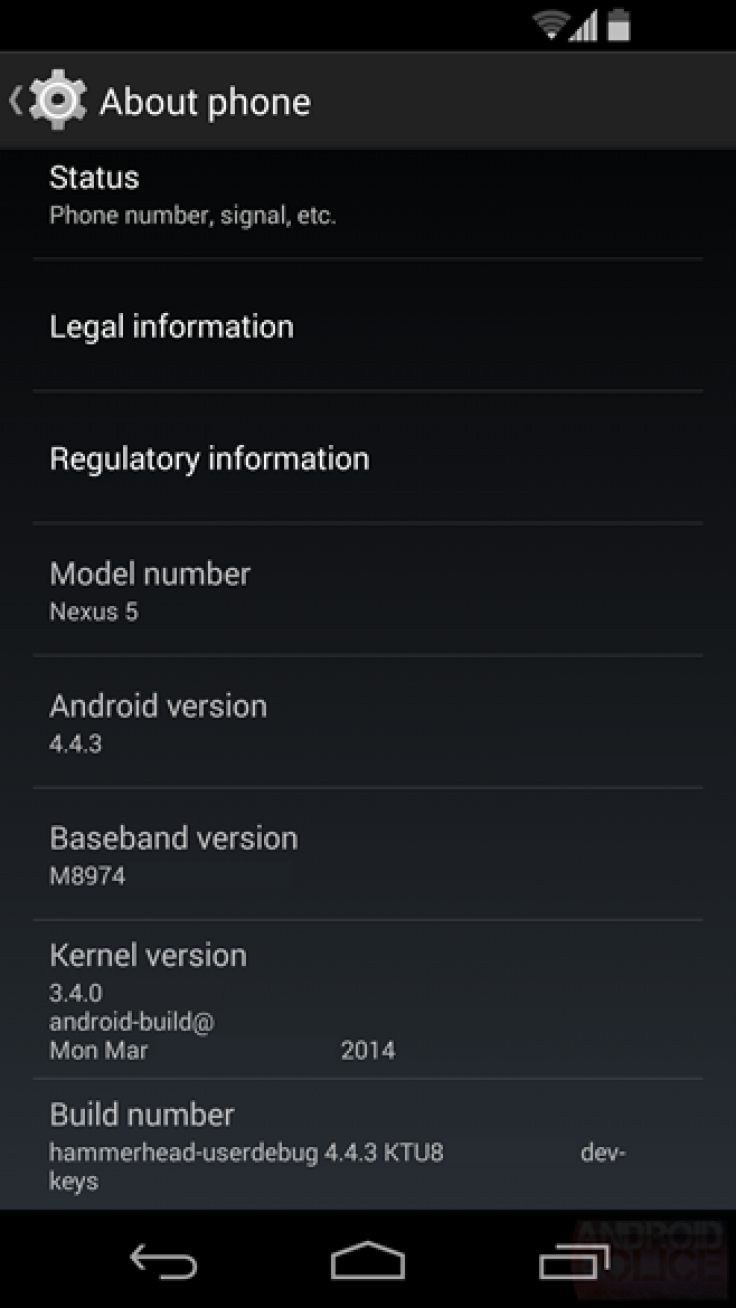
Tech website Android Police, recently shared information about the next update, which according to an accompanying screenshot of the settings page, will be Android 4.4.3 KitKat. Previous reports have speculated that the update will likely be a patch update filled with various bug fixes, and the leaked change log more or less confirms this. Users should keep in mind that even when information about future builds is leaked; many listed features may not actually show up in a final released build. Even so, here are some of the fixes that we may see from Android 4.4.3.
Leaked Android 4.4.3 KitKat Changelog [Android Police].
Frequent data connection dropout fix
mm-qcamera-daemon crash and optimization fixes
Camera focus in regular and HDR modes fixes
Power Manager display wakelock fix
Multiple Bluetooth fixes
Fix for a random reboot
App shortcuts sometimes got removed from launcher after update
USB debugging security fix
App shortcuts security fix
Wi-Fi auto-connect fix
Other camera fixes
MMS, Email/Exchange, Calendar, People/Dialer/Contacts, DSP, IPv6, VPN fixes
Stuck in activation screen fix
Missed call LED fix
Subtitle fixes
Data usage graph fix
Internet telephony fix
FCC compliance fix
Miscellaneous fixes
It has been some time since Google pushed out Android 4.4.1, and soon after Android 4.4.2. Android 4.4.2 has been the system version largely pushed onto several OEM devices as they receive the highly anticipated KitKat update. However, Nexus users appear to report the most issues with the firmware. With the incremental update, many users hope to see a resolution to issues with the Nexus 5 camera; the lens’ inability to focus and a bluish tint in the presence of white light, are among users’ main complaints. Other glitches users hope to see resolved include Bluetooth and data connection problems as well as various battery draining issues.
As said, there has been lots of talk about the next Android 4.4 build as of late and in recent weeks several build numbers, potentially connected to Android 4.4.3, have been leaked. Last week, the build number KUT72B was discovered by Italian tech website TuttoAndroid. Informant LlabTooFeR also detailed that system for that build number was under testing and that the corresponding firmware would likely include a fix for a known camera bug, which contributes to battery drain in Android devices using a Qualcomm chipset.
The issue is localized within the mm-qcamera-daemon system code, which allows third party apps (like Snapchat or Skype) access to a device’s camera. The mm-qcamera-daemon process continues to run even when those apps are closed and contributes to battery drain. Google commented on the matter in early-March saying that a fix will be “included in the next maintenance update,” but has not given a time line as to when that update can be expected.
Prior to that build leak, tech website Myce discovered the build number KTU65, which it broke down by letter and determined was a fairly recent build. Myce connected the build with KitKat before others had specified Android 4.4.3.
If we take the build string KTU65, the codename starts with the expected ’K', for Kitkat the second letter is a ‘T’, although Google has used many different letters in that position. The ‘U’ and the numbers next to it should identify the quarter, and as expected ‘U’ is Q1 2014. The 65 means the 65th day of Q1 2014, which makes it the 6th of March 2014, which means a relative new Android build.
Notably, the build number listed in the Android 4.4.3 settings screen shot also begins with KTU, indicating that the finally released build may hold a number of the same series.
© Copyright IBTimes 2024. All rights reserved.












