NSA PRISM: Don't Be Shocked, Government Surveillance Isn't Anything New

After Edward Snowden leaked information about the NSA PRISM surveillance program to the Guardian on June 27, everyone on the web responded with shock and outrage, but why is everyone so surprised that the government has that sort of program and why is everyone suddenly so concerned about privacy?
While the outrage at the United States government's overstepping of its constitutional bounds persists, one can't help but wonder why everyone has decided that, now, they seriously care about privacy and surveillance? After all, this kind of wide-reaching surveillance has been going on -- and has been reported on -- since the early 2000s. Moreover, millions of people over-share their information across social media platforms every day.
In 2006, Wired magazine published a story about a secret NSA room at an AT&T facility, room 641A, whose details were leaked by a former AT&T technician, Mark Klein, after he learned about the purpose of the room while working at the facility. Klein alleged that AT&T cooperated with the NSA, using fiber optics and a piece of hardware known as a “splitter,” which routed all Internet communications passing through the facility into the room, where data was copied and sent, while Internet traffic continued on to its final destination.
According to the Electronic Frontier Foundation, or EFF, more of these rooms existed in at least 15 to 20 AT&T facilities. With the recent leak by Snowden of documents about PRISM and other NSA programs, it has become clear that Klein’s findings were correct.
“This is a complete vindication,” Klein told Wired, referring to the leaked information. Despite these revelations and findings, there hasn’t exactly been a slowdown of information sharing on the Web.
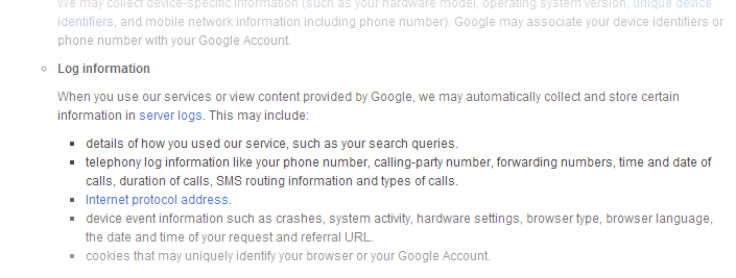
The question thus raised is: Did we really think somebody wouldn’t find a way to use all of the data we’ve uploaded onto the Internet? Google, Facebook and countless ad-serving platforms have a goldmine of data, gleaned from tracking what we search for, what we like, and even how long we stay on a page, using a combination of web browser cookies and other tracking methods. Ever read the “terms of service” while signing up for a website?
Neither do most of us. But chances are the terms will have a clause that says the company has the right to track you. One of the pieces of hardware referenced in Klein’s discovery, the Narus Semantic Traffic Analyzer, can even reconstruct data that passes through it.
“We can reconstruct all of their emails along with attachments, see what web pages they clicked on, we can reconstruct their (voice over Internet protocol) calls,” Steve Bannerman, marketing vice president of Narus, told Wired.
Even with these tracking methods, the emphasis on web privacy was much different a little over a decade ago. Some people chose to share their real identities, but more often than not, Internet users opted for pseudonyms or screen names. You’d see account names such as “proballer87” or “Xx_32Angel23_xX” and other variants that were unique but not necessarily something that would compromise your anonymity.
Then social media happened. Instead of staying anonymous, people started using their real names. Users share pictures on Twitter, their location on Foursquare, and provide an easy-to-access list of people they've interacted with on Facebook -- not to mention the drunken pictures and countless unfiltered comments on YouTube tied to real names that make you want to pretend that comment threads don’t even exist for the content you’re looking at.
While it’s right to argue that the right to have the choice to share or not share information is paramount to privacy, a vast majority of the Internet does a poor job at limiting this oversharing of information. I'm not arguing that we should just let it be, or that we shouldn’t care about broad, encroaching government surveillance. But it’s useless to complain about these things and do nothing about them.
If that means encrypting your hard drives, then do so. Both Windows and OSX have features built in that allow for that in technologies like BitLocker and FileVault. Use encrypted chat protocols, or if you’re really paranoid, even consider using a prepaid phone. If you use Twitter or Foursquare, it might not be the smartest thing to tweet your every location or make your home a place to “check in” to.
Try doing a Google search of yourself. If there’s information about you there, don’t be surprised if somebody is using it somewhere, somehow. Don’t expect your government to give you back your privacy. Take it back. You can also take a look at some of the evidence regarding this secret room in the document below.
© Copyright IBTimes 2024. All rights reserved.












