McAfee: Android Phones on Top of Malware Hit List, Q3 Report Reveals Threats on the Rise
Intel-owned security technology firm McAfee has released its third quarter security threats report, which revealed that malware targeted at phones running Google's Android Operating System (OS) are increasing.
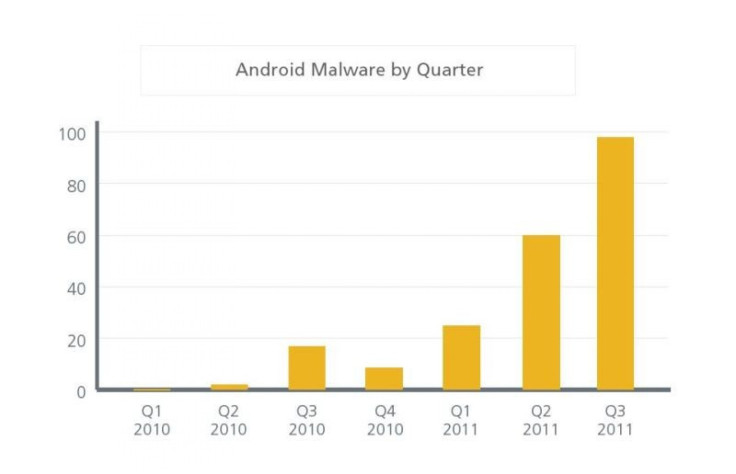
The report said the Android OS solidified its dubious lead as the primary target for new mobile malware. Since the previous quarter, the amount of malware targeted at Android devices has increased nearly 37 percent, putting 2011 on track to be the busiest in mobile and general malware history. Nearly all new mobile malware in Q3 was targeted at Android, according to the report.
McAfee said both general and mobile malware were more prevalent than ever in the third quarter.
So far this year, we've seen many interesting yet challenging trends that are affecting the threat landscape, including heightened levels of sophistication and high-profile hacktivist attacks, said Vincent Weafer, Senior Vice President of McAfee Labs.
McAfee predicted, at the end of 2010, that malware would touch 70 million unique samples by the end of 2011. However, due to rapid production of malware this year, the prediction has been increased to 75 million unique malware samples by year's end, which is the busiest in malware history, said McAfee.
While Symbian remains the platform with the most number of malwares, Android became the most popular platform for new malware in the quarter.
The security firm said Malware authors were eyeing the Android platform because of its popularity.
One of the most popular forms of trickery in Q3 was a SMS-sending Trojan that collected personal information and stole money. There was another malware for stealing user information that could record phone conversations and forward them to the attacker.
According to the report, commonplace security threats are also on the rise. Fake Anti-Virus (AV), AutoRun and password-stealing Trojans have bounced back strongly from previous quarters, while AutoRun and passwords stealers stayed comparatively steady. Mac malware also continued to grow in Q3, though not as quickly as it did in the previous quarter.
Web threats were also a common way for attackers to prey on unsuspecting victims. In Q3, the number of new bad sites dropped to 6,500 from an average of 7,300 in Q2.
While spam remained at its lowest levels since 2007, spearphishing, or targeted spam, was at its greatest in years. While the idea may not be prominent, it is highly sophisticated and effective.
According to the report, overall botnet infections dropped slightly in Q3 but they seemed to have increased significantly in Argentina, Indonesia, Russia and Venezuela.
Social engineering was used to lure targets, particularly those that depended greatly on geography and language. In the U.S., Delivery Service Notifications (or fake error messages) were the most popular, while in the UK 419 scams reigned supreme. In France, phishing scams dominated, while drug spam was the most popular lure in Russia.
Regarding hacktivist attacks, the report said that the idea of these kinds of attacks were not abundantly transparent in Q3, as compared to past quarters. The report highlighted hacktivist activity from Q3, with at least 10 high-profile attacks at the hands of Anonymous, including attacks against the Arizona Fraternal Order of Police, Booz Allen Hamilton, Bay Area Rapid Transit, Austrian Police and Goldman Sachs.
© Copyright IBTimes 2024. All rights reserved.












