Nuclear Power Plants Around The World Unprepared For Cyberattacks, Warns New Report

Nuclear power plants across the world are getting increasingly vulnerable to cyberattacks as they increase their reliance on digital systems and “off-the-shelf” software, Chatham House -- a London-based nonprofit -- warned, in a new report. Moreover, because of an “element of denial,” several nuclear facilities have failed to put in place mechanisms to protect themselves against digital attacks.
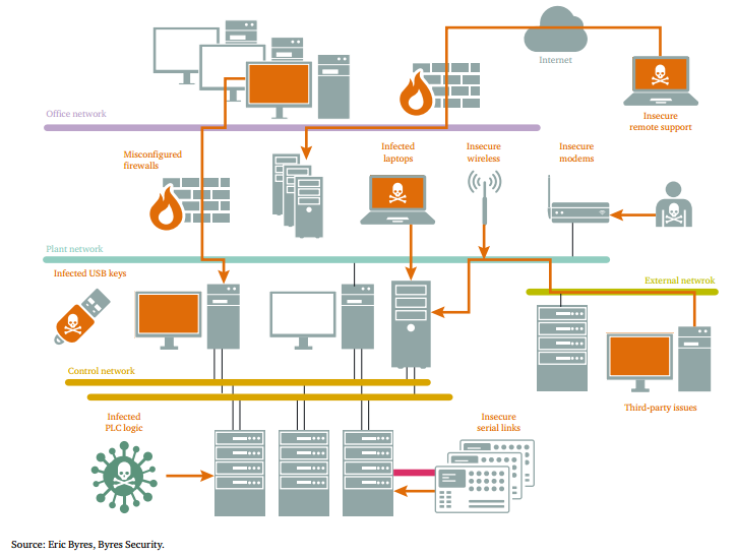
“There is a pervading myth that nuclear facilities are ‘air gapped’ -- or completely isolated from the public internet -- and that this protects them from cyber attack,” the report, which analyzed cyber defenses in power plants across the world in an 18-month period, said. “Yet not only can air gaps be breached with nothing more than a flash drive, but the commercial benefits of internet connectivity mean that nuclear facilities may now have virtual private networks and other connections installed, sometimes undocumented or forgotten by contractors and other legitimate third party operators.”
The report noted that the Stuxnet computer virus -- discovered in 2010 after having successfully infected Iran’s nuclear facilities -- had been uploaded through a flash drive.
In addition, even as vulnerability of nuclear power plants increases -- partly because of their outdated control systems -- hacking is becoming even easier to conduct with the availability of automatic cyberattack packages that can be purchased online.
In some cases, the lack of cybersecurity is particularly glaring. Officials interviewed for the report said that some nuclear facilities did not even bother changing the default passwords on their computer systems. As a result, hackers can gain access to nuclear facilities more easily than it should be possible -- just by entering a standard factory-set password such as 1234.
“The infrequency of cyber security incident disclosure at nuclear facilities makes it difficult to assess the true extent of the problem and may lead nuclear industry personnel to believe that there are few incidents,” the report found, identifying it as a major industry-wide challenge. “Moreover, limited collaboration with other industries or information-sharing means that the nuclear industry tends not to learn from other industries that are more advanced in this field.”

In order to protect themselves from potentially deadly cyberattacks, the civil nuclear sector needs to work on an international cybersecurity risk management strategy that ensures a flexible and coordinated response, the report recommended.
“The cybersecurity threat requires an organizational response by the civil nuclear sector, which includes, by necessity, knowledgeable leadership at the highest levels, and dynamic contributions by management, staff and the wider community of stakeholders, including members of the security and safety communities,” the report said.
© Copyright IBTimes 2024. All rights reserved.












