US Intelligence Chief Clapper Skeptical On US-China Cyber Deal
By Andrea Shalal
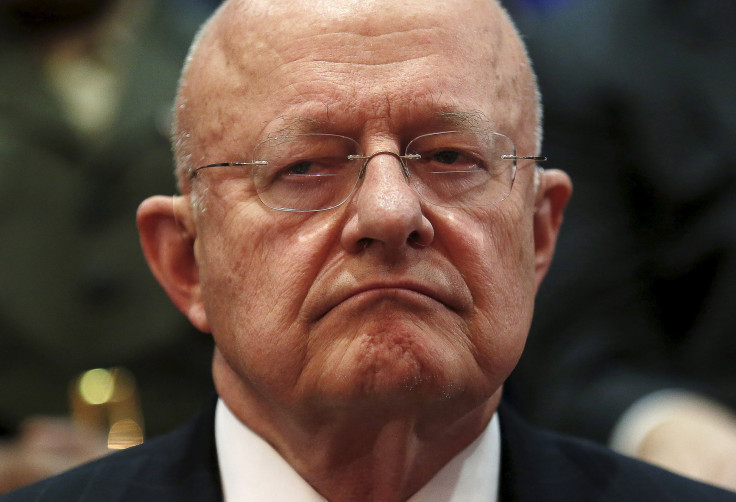
WASHINGTON (Reuters) -- The top U.S. intelligence official said he was skeptical that a new U.S.-China cyber agreement would slow a growing torrent of cyber attacks on U.S. computer networks, adding that his approach will be to "trust but verify."
Director of National Intelligence James Clapper told the Senate Armed Services Committee on Tuesday that the agreement did not include specific penalties for violations but that the U.S. government could use economic sanctions and other tools to respond if needed.
Clapper and other officials said they viewed last week's cyber agreement between Chinaand the United States on curbing economic cyber espionage as a "good first step" but noted it was not clear how effective the pact would be.
President Barack Obama said on Friday that he had reached a "common understanding" with China's President Xi Jinping that neither government would knowingly support cyber theft of corporate secrets or business information.
Asked if he was optimistic the agreement would eliminate Chinese cyber attacks, Clapper said simply: "No."
Clapper said he was skeptical because Chinese cyber espionage aimed at extracting U.S. intellectual property was so pervasive, and there were questions about the extent to which it was orchestrated by the Chinese government.
He said the United States should "trust but verify," a reference to former President Ronald Reagan's approach to nuclear disarmament with the former Soviet Union.
Clapper and other top U.S. military officials said cyber threats were increasing in frequency, scale, sophistication and severity, and the United States needed the same kind of deterrent capability in cyberspace that it maintains for nuclear weapons.
Attacks by countries such as Russia, China, Iran and North Korea, as well as non-state actors, would increase and likely grow more sophisticated in coming years, expanding to include manipulation of data, he said.
"Such malicious cyber activity will continue and probably accelerate until we establish and demonstrate the capability to deter malicious state-sponsored cyber activity," he said. Establishing a credible deterrent requires agreement on norms of cyber behavior by the international community, he said.
However, they said attributing a cyber attack was far more difficult than determining who launched a missile.
Clapper said the current environment was like "the Wild West" and the world needed to deal with the evolving threats.
One key question, he said, was whether to limit spying activity, such as the incident that compromised personal data of 21 million individuals in a database maintained by the Office Of Personnel Management.
Deputy Defense Secretary Robert Work told the committee that the U.S. response would be "vigorous" if another incident on the scale of the OPM breach was firmly linked toChina. He said the Pentagon was finalizing a broad cyber warfare policy that was supposed to have been shared with Congress over a year ago.
He said the response could involve a variety of tools, including economic sanctions and criminal indictments, as well as potential use of offensive cyber weapons.
U.S. officials have linked the OPM breach to China, but have not said whether they believe its government was responsible.
Clapper said no definite statement had been made about the origin of the OPM hack since officials were not fully confident about the three types of evidence that were needed to link an attack to a given country: the geographic point of origin, the identity of the "actual perpetrator doing the keystrokes," and who was responsible for directing the act.
Separately, the four-star general leading the U.S. military command that transports troops and cargo told Reuters that he was concerned about cyber attacks on its contractors and industry partners.
Air Force General Darren McDew, who heads the U.S. Transportation Command, said that while efforts had been made to improve the command’s cyber security, his "concern is outside of that sphere". He added that the protection of U.S. defense contractors "is not as robust".
A little over a year ago, a Senate Armed Services Committee report said the Transportation Command’s computer systems had been breached at least 20 times in a year and cast doubt about the security measures being undertaken.
(Additional reporting by Idrees Ali.; Editing by Chizu Nomiyama, Christian Plumb and Ken Wills)
© Copyright Thomson Reuters 2024. All rights reserved.











