What Is Unflod.dylib? Malicious iOS Jailbreak Software Steals Apple ID And Passwords From Unsuspecting Users; How To Remove Malware

A new piece of malware is making its way around jailbroken Apple Inc. (Nasdaq:AAPL) iOS devices, attempting to steal Apple IDs and passwords.
The malicious piece of software, “Unflod.dylib,” was discovered on some jailbroken Apple iOS devices on Thursday by Reddit users after a user complained that the file was causing apps such as Snapchat and Google Hangouts to crash constantly. Soon after the thread was started, several developers in the Reddit jailbreak community told the user to not touch the software, which they suspected was malware.
When the jailbreak developers inspected the “Unflod.dylib” file, they discovered that the malicious software captures Apple IDs and passwords from Internet sessions that use Secure Socket Layer (SSL) to encrypt communications and then sends the login information to the Internet Protocol (IP) address “23.88.10.4.”
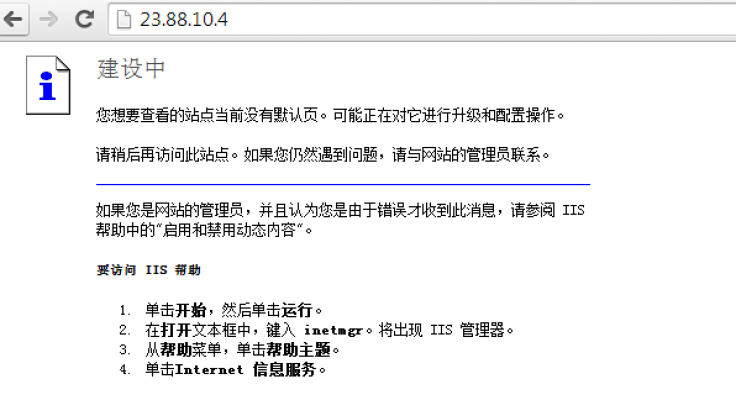
While the exact origin of the malicious software has yet to be discovered, users speculate that the software may be of Chinese origin due to the error page displayed when visiting the IP address discovered in the code and a developer certificate digitally signed by the name Wang Xin. Other theories currently floating around speculate that the software may have been installed through software obtained through a Chinese piracy app repository. However, this is currently unconfirmed.
What Apple iOS Devices Are Affected?
The users of the latest 64-bit iOS devices such as the iPhone 5S, iPad Air and iPad Mini Retina might not be affected the malware if it is present on the device. However, those running iPhone 5 and any other 32-bit jailbroken iOS device have been advised by jailbreak developers to check their devices for the malicious software using file browsers such as iFile, which is available on the Cydia Store.
Note: International Business Times is not responsible for any damage caused by running any unofficial software, tweaks or modifications on your jailbroken iOS device. Proceed at your own risk.
If the “Unflod.dylib” malicious software is present on a jailbroken iOS device, it can be found in this directory:
“/Library/MobileSubstrate/DynamicLibraries/”
How to Remove The Malicious Software
Should the Unflod.dylib file be found in that directory, iOS developer, Saurik, has compiled complete instructions on how to remove the malware, which can be read here.
For a more technical analysis of “Unflod.dylib,” take a look at the blog entry about the malicious code posted on SektionEins.
Users affected by the malicious software are also advised to change their Apple ID password after the software is removed.
© Copyright IBTimes 2024. All rights reserved.












