What is Pentagon doing to stop secret file leaks in future?
The Pentagon on Sunday condemned the latest publication of hundreds of thousands of sensitive classified documents by WikiLeaks and unveiled various measures to stop future disclosures of secret files.
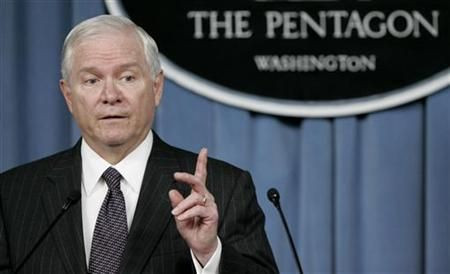
As we have in the past, we condemn this reckless disclosure of classified information illegally obtained, said Bryan Whitman, Pentagon spokesman.
Following the whistle-blower website's release of 250,000 diplomatic cables to The New York Times and some other newspapers on Sunday, the U.S. Defense Department (DoD) highlighted a series of measures carried out in recent months to thwart the leakage of sensitive data.
The defense department had ordered two reviews of information and intelligence sharing in August after Wikileaks disclosed tens of thousands of US military intelligence files on the war in Afghanistan.
The DoD had disabled all “write” capability for removable media on classified computers to mitigate the risks of personnel moving classified data to unclassified systems.
Steps also directed DoD organizations to have a limited number of systems authorized to move data from classified to unclassified systems.
To ensure proper oversight and reduce chances of unauthorized release of classified material, DoD organizations are now also implementing two-person handling rules for moving data from classified to unclassified systems, Whitman said.
The DoD is also monitoring suspicious activity similar to the ways followed by credit card companies, Whitman said. Some 60 percent of DoD’s classified net is now using a host-based security system – an automated way of controlling the computer system with a capability of monitoring unusual data access or usage. The department is speeding deployment to the rest of the classified system, Whitman said.
U.S. Central Command also has established insider threat working groups to address the Wikileaks incident and prevent reoccurrence.
“It is now much more difficult for a determined actor to get access to and move information outside of authorized channels, Whitman said.
© Copyright IBTimes 2025. All rights reserved.





















