Is Equifax Data On The Dark Web? Not Yet, But It Will Be

Following the security breach of credit reporting firm Equifax that resulted in the personal information of an upwards of 143 million Americans being stolen, researchers are searching to find who executed the hack and where the stolen data will end up—though thus far the clues have been sparse.
With any data breach, but especially one the size of the Equifax incident, it seems inevitable that the stolen information will end up on the dark web—either sold off to the highest bidder or in bits and pieces that allow black market buyers to purchase and use stolen information.
In the case of the Equifax hack, there is plenty of personal information to go around. The credit reporting firm said Thursday the credit card numbers of approximately 209,000 consumers in the United States were accessed by an unauthorized source. It also confirmed the hackers gained access to the personally identifying information of 182,000 U.S. consumers.

The breach is feared to be much wider than that, and likely includes Social Security numbers among other pieces of sensitive information. As many as 143 million in the U.S. could be affected, as well as some consumers in the United Kingdom and Canada.
That information all has particular value on the dark web, and experts believe it’s more than likely the information will appear there in the future.
“We expect it is only a matter of when, not if, this data appears on the Dark Web market,” Ondrej Vlcek, chief technology officer and general manager of consumer business at security firm Avast, told International Business Times.
Similarly, director of analysis at data intelligence firm Terbium Labs Emily Wilson said, “we absolutely expect to see this information appear on the dark web in the future.”
While the release of the data online seems to be a certainty, in the immediate wake of the hack the data is yet to be seen.
The first potential lead appeared early Friday when a dark website called BadTouch appeared online and claimed to be selling a database of data stolen from Equifax.
The site was set up by an apparent duo of hackers who identify themselves as the PastHole Hacking Team. The collective claims to have access to personally identifying information of more than 140 million people—including social security numbers, driver’s license numbers, dates of birth and addresses—as well as more than 200,000 credit card numbers.
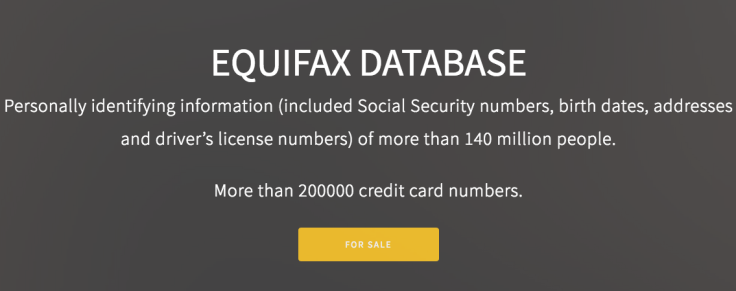
According to the site, the two supposed hackers identified themselves as just “two people trying to solve our lives and those of our families.” The hacking team claimed to have not expected to gather as much information as they did and have no intention of affecting any individuals but intend to “monetize the information as soon as possible.
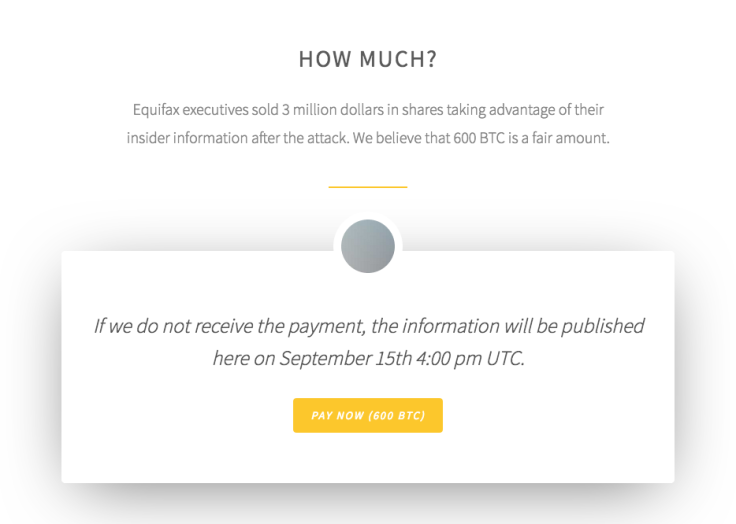
As such, the PastHole team said they were looking for 600 Bitcoin (about $2.6 million) in exchange for the database—a price set based on the nearly $2 million made by Equifax executives who sold shares in the company after the breach was discovered but before it was disclosed to the public.
The demand appears to be an attempt at extorting Equifax, as the group claims to only be interested in talking to “managers and employees” of the company. The alleged hackers claim that if the amount is paid, “all the information and all the backups will be deleted.”
According to PastHole, they will publish the information at 12 p.m. EDT on Sept. 15 if payment is not received.
While PastHole was the first to claim possession of the stolen information from Equifax, there is little to verify the legitimacy of the claim. The group has no history to speak of, which not necessarily indicative of the group’s capabilities but makes it harder to attest to their legitimacy.
While the group listed an email address and PGP key on its website, they have thus far been unresponsive to any attempts to reach them. The group also has not provided a sample of data despite offering to do so on its website.
Terbium Labs’ Wilson told IBT her company is monitoring the situation but said, “At this time no samples have surfaced yet of this data to attest to its validity.”
After PastHole’s website appeared on the dark web, another person laying claim to the Equifax database appeared online. On Twitter, a user identifying as an “underground researcher” known as 1x0123 claimed to be in possession of the personal information stolen from the credit reporting firm.
Unlike the PastHole Hacking Team, 1x0123 does have history to lean on. The researcher has reported security vulnerabilities in the past and was even thanked whistleblower Edward Snowden for reporting a security hole on affecting the Freedom of the Press Foundation.
Despite 1x0123’s history, it seems the claim over the Equifax database may be bunk. When IBT asked for confirmation the information was authentic, 1x0123 declined to provide any proof without payment. “Nothing is free,” the hacker said.
When asked to provide a sample of the dataset to test its veracity, 1x0123 demanded between $500 to $1,000 to be paid in Bitcoin before providing any sort of evidence. The hacker also declined to provide any additional screenshots of the supposed database.
1x0123 insisted the database was real and said any buyer hoping to purchase the massive collection of personal information stolen from Equifax would have to pay 40,000 Bitcoin—or about $173.5 million. The hacker also claimed the PastHole Hacking Team were “scammers” and “kids.”
A security researcher on Twitter who goes by x0rz decried 1x0123 as a fraud and said the supposed hacker blocked him after calling him out on the claims. Others likewise have questioned the legitimacy of the hacker.
While the early claims of access to the Equifax database appear untrue—or at the very least unverifiable—that doesn’t mean the information won’t appear online. It’s far too big of a score containing too much actionable information for someone not to try to profit off it.
Patrick Tiquet, director of security and architecture at Keeper Security, told IBT driver’s license numbers typically sell online for $20 and Social Security numbers go for $1. “If each of the 143 million users that were affected lost both of these documents, the cybercriminals that are selling this information could make an upwards of $2 billion - and that is just the base level,” he said.
An analysis of the database by security firm Trend Micro made a much more conservative estimate but still found the dataset could be worth more than $27 million if sold on the dark web—a figure based on the lowest estimated prices such data might be sold for.
Wilson noted the database is valuable “because of what it is, not because of where it came from.” As such, the information is likely to be sold even if it isn’t advertised as part of the newsworthy breach.
“It's entirely possible we'll see this data circulate without ever being identified as the Equifax breach, just as much as we would expect vendors on the dark web to capitalize on the publicity around this breach to pawn off old, unrelated data,” Wilson said.
© Copyright IBTimes 2024. All rights reserved.




















