Cyber Criminals Are Getting More Sophisticated, So Watch Out For These New Scams In 2014

Cyberattacks drew a lot of press in 2013, from the wholesale theft of millions of classified documents by rogue NSA staffer and international fugitive Edward Snowden to the exposure or theft of credit card numbers and other personal data. And it looks like we're in for more.
"Bypassing traditional defenses was raised to an art form by cybercriminals in 2013," said Charles Renert, vice president of security research for Websense, which released a report on the subject and predictions for 2014.
And in another study, the World Economic Forum warned that intensifying cyber threats will be one of the top trends of 2014.
"Rather than attempting to prevent all possible forms of hacking, governments, private firms and NGOs should ensure that it’s not catastrophic to get hacked," the World Economic Forum report concluded.
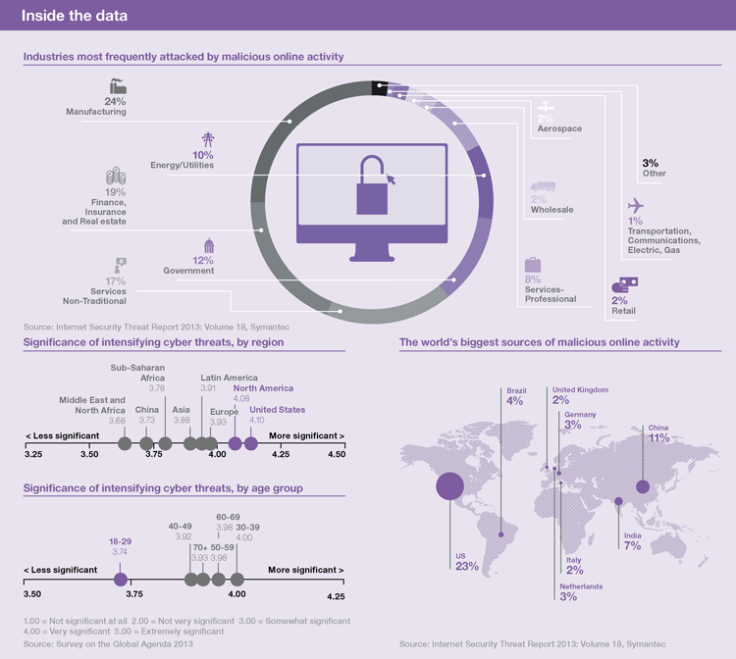
The group also published this clever chart showing the state of cybersecurity.
"In 2014, cyberattacks will be even more complex and diverse. While the general volume of advanced malware will decrease, we predict the volume of targeted attacks and data destruction incidents will increase. Organizations must up their security game as attackers continue to seek new ways to penetrate traditional defenses at every stage of the threat life-cycle," the report said.
Here are 8 security predictions from Websense for 2014:
1. Advanced malware volume will decrease. According to the real-time telemetry feeds in Websense ThreatSeeker® Intelligence Cloud, the quantity of new malware is beginning to decline. Unfortunately, this is bad news for organizations.
Cybercriminals will rely less on high-volume advanced malware, because over time it runs a higher risk of detection. They will instead: use lower volume and more-targeted attacks to secure a foothold; steal user credentials; and move unilaterally throughout infiltrated networks. Although the volume of attacks will decrease, the risk is even greater.
2. A major data-destruction attack will happen. Historically, most attackers have used a network breach to steal information for profit. In 2014, organizations need to be concerned about nation-states and cybercriminals using a breach to destroy data. Ransomware will play a part in this trend and move down-market to small- and medium-sized organizations.
3. Attackers will be more interested in cloud data than your network. Cybercriminals will focus their attacks more on data stored in the cloud vs. data stored on the network. This tactical shift follows the movement of critical business data to cloud-based solutions. Hackers will find that penetrating the data-rich cloud can be easier and more profitable than getting through the "castle walls" of an on-premise enterprise network.
4. Redkit, Neutrino and other exploit kits will struggle for power in the wake of the Blackhole author arrest. The Blackhole exploit kit was arguably the most successful in history. Everything changed in October 2013 when "Paunch," the alleged hacker author behind the famous kit, was arrested in Russia. We will see a fight for market leadership between a number of new entrants and existing exploit kits in 2014. We anticipate Redkit and the Neutrino exploit kit will secure a strong foothold in the coming year.
5. Java will remain highly exploitable and highly exploited—with expanded repercussions. Most end points will continue to run older versions of Java and therefore remain extremely exposed to exploitation. In 2014, cybercriminals will devote more time to finding new uses for tried-and-true attacks and crafting other aspects of advanced, multistage attacks. Attackers will reserve zero-day Java exploits for targeting high-value networks with good Java-patching practices.
6. Attackers will increasingly lure executives and compromise organizations via professional social networks. As social networking continues to appeal to the business community in 2014, attackers will increasingly use professional websites, such as LinkedIn, to research and lure executives. This highly targeted method will be used to gather intelligence and compromise networks.
7. Cybercriminals will target the weakest links in the "data-exchange chain." Attackers will go after the weakest links in the information chain and target the consultants outside the network who have the most information. This includes consultants, contractors, vendors and others who typically share sensitive information with the large corporate and government entities. And, it turns out, few of these partners have sufficient defenses.
8. Mistakes will be made in "offensive" security due to misattribution of an attack's source. For several years, we've been hearing more about "offensive" security, where global governments and enterprises have been threatening retaliatory strikes against anyone caught attacking them or their interests. As in traditional warfare, tactical mistakes will increasingly happen in these cybertrenches. Failure to accurately identify a cyberperpetrator could result in an innocent organization being caught in the crossfire.
© Copyright IBTimes 2025. All rights reserved.





















