Edward Snowden Reveals 'Quantum Insert': NSA And GCHQ Used Fake LinkedIn And Slashdot Pages To Install Spyware

The latest leak to come from the former NSA contractor-turned-whistleblower Edward Snowden revealed that the British intelligence agency GCHQ used fake LinkedIn and Slashdot pages to plant malware within a Belgian telecommunications company.
German newspaper Der Spiegel reported that documents leaked by Snowden show that the GCHQ used a method called “quantum insert” to redirect employees of Belgacom, Belgium’s largest telecommunications company, to fake websites that contained spyware. The program targeted higher-level employees that had “good access” to Belgacom’s infrastructure.
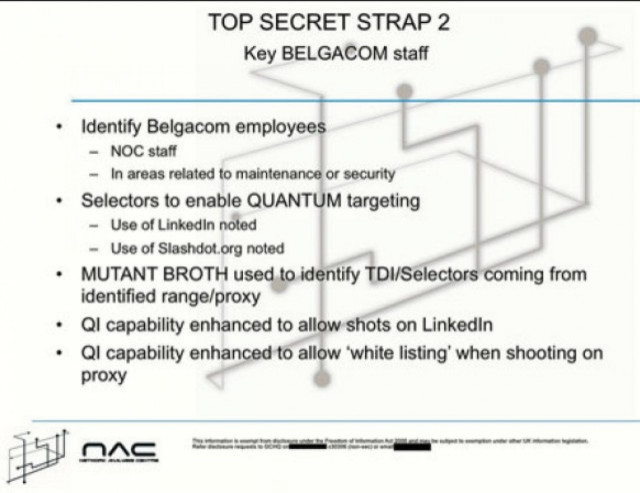
It was revealed back in September that both the NSA and the GCHQ were using the “quantum insert” method, also known as a “man in the middle attack,” to “enable better exploitation” of Belgacom, but creating fake versions on LinkedIn and Slashdot takes the plot a step further.
Belgacom is a Global Roaming Exchange provider, which handles mobile Internet traffic for users traveling internationally. Der Spiegel also reported that the GCHQ and NSA also targeted employees of the Organization of Petroleum Exporting Countries, the global oil cartel.
LinkedIn denied any knowledge of the program and that it “would never approve such activity.”
© Copyright IBTimes 2025. All rights reserved.






















