Largest Ransomware Paid: South Korean Web Host Pays More Than $1M After Attack
South Korean web hosting company Nayana paid more than $1 million after its servers were hit by a massive ransomware attack.
The ransomware spread to more than 153 of Nayana’s servers, making the files inaccessible. It also affected more than 3,400 websites hosted by the company—many of which were websites for businesses.
The attackers initially demanded 550 bitcoin (about $1.6 million at the time) to end the attack. In a message sent from the attackers to Nayana, the hosting company was told, “If you cannot pay that, you should go bankrupt.”
Nayana eventually negotiated the price down to 397.6 Bitcoins, or slightly more than $1 million. It is believed to be the largest ransom ever extorted from such an attack. The amount was to be paid in three installments and required Nayana to sell shares of its company to another party in order to raise the funds.
Since paying the ransom, Nayana is still attempting to restore operations back to normal. Some of its customers still do not have their websites back online, though the hosting company has been providing regular updates on its own site.
While the attack has been particularly devastating, both to Nayana and its customers, it also reveals just how important taking basic security precautions can be in avoiding extensive damage—both monetarily and in terms of lost data.
Read: Cyberattacks: Phishing, Ransomware Attacks Rose In 2016, Symantec Reports
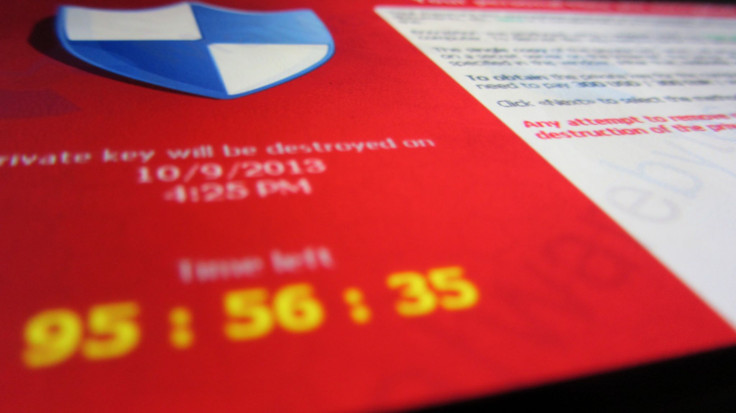
Security researchers have indicated they believe Nayana was hit by a Linux variant of the Erebus ransomware. The attack is designed to target files on web servers, encrypting the data to make it impossible to access and demanding a payment to restore the files. The Erebus ransomware has also been heavily concentrated in South Korea in its attacks.
How the ransomware invaded Nayana’s servers isn’t entirely clear, though a report from security firm Trend Micro found the web hosting company appeared to have left its servers unpatched for several years, leaving Nayana vulnerable to attack.
Security patches are often made available for well-known exploits, and a failure to install those patches means those known exploits can be used against the unpatched system. A similar failure to update led to the global WannaCry ransomware attack that exploited a vulnerability in Windows despite a patch being available for it.
In that case, the United States National Security Agency came to Microsoft to alert it of the vulnerability —which the agency had been exploiting for its own purposes for several years only to make public after the tools used to exploit it were stolen by a hacking group. Microsoft issued a patch in March that fixed the vulnerability, but most machines still hadn’t updated by the time the attack spread in May.
The attack also shows the importance of maintaining backups. While Nayana has insisted to its customers that it maintained “double backup” of all of its files, the company has been unable to fully restore its capability.
Ransomware has been on the rise, as have the ransom costs associated with the attacks. Businesses and individuals can avoid some of the risks by taking proper precautions including regularly downloading security updates and keeping backups of important files.
© Copyright IBTimes 2024. All rights reserved.











