Samsung Galaxy S3 Security Bug Discovered, Bypasses Lockscreen And Allows Full Access To Device [VIDEO]
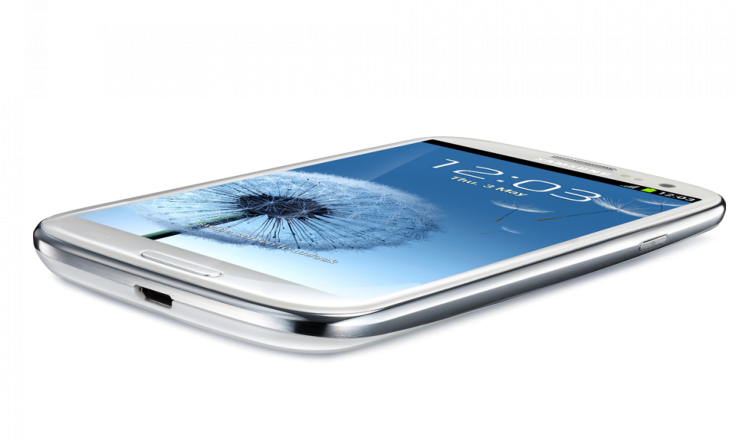
Samsung Galaxy S3 owners should keep a closer eye on their handsets as a serious security bug has been discovered on 2012’s favorite Android smartphone.
The flaw, revealed by Sean McMillan on the Full Disclosure mailing list, is a method of bypassing the Galaxy S3’s lockscreen, which can allow potential intruders full access to the device in a series of steps that is particularly simple to remember.
As per McMillian’s instruction, someone can bypass a Galaxy S3 lockscreen in five steps:
- Tap Emergency call on the lock screen.
- Tap the ICE -- emergency contacts button.
- Press the Home button once.
- Immediately press the power button after performing step 3.
- If the bug has occurred, pressing the power button the second time directs you to the home screen.
The process of maliciously unlocking a Galaxy S3 is actually somewhat difficult, according to CNET. The business website admits its team was not able to replicate the bug, but other publications like Engadget reported being able to bypass the lockscreen after several attempts. McMillian himself noted that it took him at least 20 tries to skirt the lockscreen on his Galaxy S3.
But once the bug is successful, the lockscreen remains disabled until the device is rebooted, according to Android Authority.
McMillian adds that the bug appears to be a flaw engrained in Samsung's software and is not an issue throughout Android-powered devices.
Just days prior, mobile enthusiast Terence Eden uncovered a bug on the Samsung Galaxy Note 2. In a similar array of steps, the device’s lockscreen can be briefly compromised and its home screen visible for a few seconds.
- Lock the device using the affected security types mentioned above.
- Turn the screen on.
- Tap Emergency call.
- Tap the ICE -- emergency contacts button on the bottom left.
- Press the Home button.
- Quickly tap on an app/widget displayed on the home screen.
If quick enough, someone can, for example, access its direct dial widget and place a call without unlocking the phone. The bug also allows other apps to be opened while the phone is still unlocked. But the apps cannot be operated; they simply continue running behind the lockscreen.
Samsung has yet to comment on the issue; however, CNET suggests the Korean-based company may tackle the bug with software updates.
This isn’t the first or second time a Samsung Galaxy series device has had a lockscreen security flaw. Following the U.S. release of the Samsung Galaxy S2 in 2011, its AT&T model was found to have a bug that allowed an easy bypass of the device’s lockscreen by simply pressing the lock button, allowing the screen to go black and pressing the lock button a second time. The flaw was present as long as the phone had been unlocked at least once with the correct pattern or PIN.
It was reported at that time that the flaw was only present on the AT&T model of the Galaxy S2 and not the Sprint Model or any international models. The T-Mobile Galaxy S2 model had not been released at that time.
Apple also had a lockscreen security flaw issue recently, where two different methods for bypassing the iOS lockscreen were discovered. The company is currently releasing its iOS 6.1.3 beta update to developers to see if it corrects the issue.
© Copyright IBTimes 2024. All rights reserved.












