Android Phones Release Confidential Contents When Frozen
Android is the world’s most popular smartphone operating system, but it’s also the least secure: Most security firms, including notables such as McAfee, Kaspersky and Sophos, all agree that Google’s little green robot is the most popular place for new malware.
While Android is exceedingly susceptible because its code is famously open source, a team of German researchers have discovered a new vulnerability in the operating system, which essentially bypasses Google’s data scrambling encryption system introduced in Android 4.0 Ice Cream Sandwich to reveal the phone’s hidden data.
Engineers at the Friedrich-Alexander University in Erlangen, Germany, released a report on Thursday that explains how freezing an Android phone can help law enforcement or forensic workers expose a scrambled Android phone’s contact lists, photos, browsing histories and more.
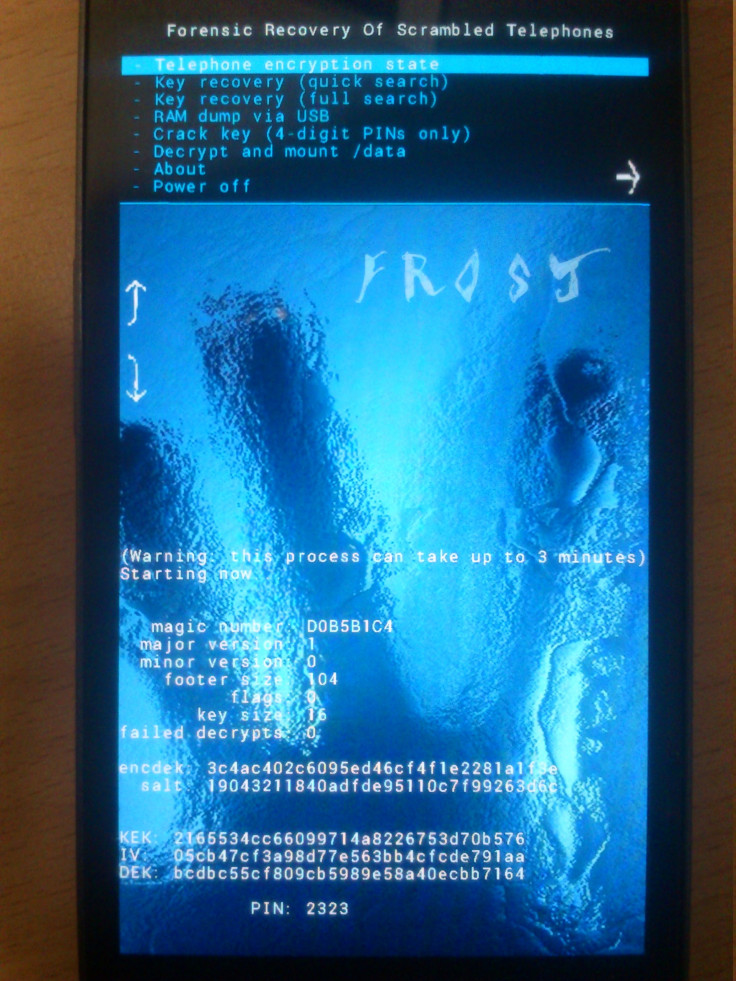
“We present Frost, a tool set that supports the forensic recovery of scrambled telephones,” the researchers said in their report’s abstract. “To this end, we perform cold boot attacks against Android smartphones and retrieve disk encryption keys from RAM. We show that cold boot attacks against Android phones are generally possible for the first time, and we perform our attacks practically against Galaxy Nexus devices from Samsung. To break disc encryption, the bootloader must be unlocked before the attack, because scrambled user partitions are wiped during unlocking. However, we show that cold boot attacks are more generic and allow to retrieve sensitive information, such as contact lists, visited Web sites and photos, directly from RAM, even though the bootloader is locked.”
In their work, FAU researchers Tilo Muller, Michael Spreitzenbarth and Felix Freiling left a locked Galaxy Nexus phone running Android 4.0 inside a -15 degree Celsius freezer for about 60 minutes.
“Cooling the device down under 10 degree Celsius increases the success of cold boot attacks considerably, because RAM contents fade away more slowly if RAM chips are cold,” the researchers said. “After an hour, the phone temperature should be below 10 degree. Note that the temperature varies with the point you measure (metal or plastic).”
Once the phone was cold enough and still operational (one can check by pressing the power button), the Android phone was ready for “cold boot attacks.” Without a reset button, however, the team had to reboot the Galaxy Nexus by disconnecting and replugging its battery in a very swift motion that lasts “less than 500ms.” Once the battery’s back in place, the FAU researchers simply held down the power button with both volume up and down buttons -- a combination that brings the Android phone into “fast boot mode,” which means researchers could flash their Frost tool directly onto the device.
The FAU researchers connected the Android phone to a Linux PC via USB, and installed the “frost.img” file to the phone. Once the operation was completed, a Recovery Mode option appears under the “fast boot” menu, which then rebooted the phone with the Frost tool. The recovery image features several options like key recovery using quick or full search options, the ability to decrypt and mount the phone’s data and crack the 4-digit PIN key with brute force (like in the photo below).
"We thought it would work, because smartphones are really small PCs," Muller told BBC. "But we were quite excited that the trick with the freezer worked so well."
Muller may be right about Android devices being similar to PCs, but, in the U.S. and Australia, Sophos says Android threat exposure rates have greatly exceeded those of PCs in 2013.
We’ve reached out to the trio of FAU researchers to learn more about whether or not the Frost tool can be applied to all Android phones running 4.0 or possibly phones even running 4.1 Jelly Bean. We will update this story as soon as we learn more.
Android currently claims 52.3 percent of all smartphone platform share, according to comScore.
© Copyright IBTimes 2024. All rights reserved.












