Cyberspies, Perhaps Operating In China, Infiltrated US Natural Gas Network: Such Cybercrime Poses More Than Virtual Threat, It’s Kinetic
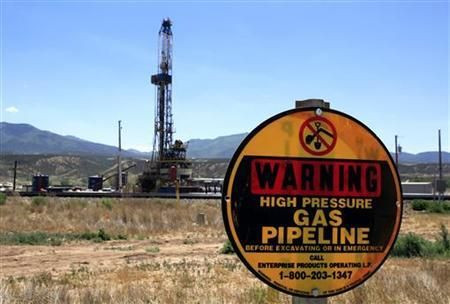
The U.S. Department of Homeland Security suspects that China is behind nearly two dozen attempts to obtain sensitive information from natural gas pipeline companies, which it says could be used potentially not just to disrupt operations but also to blow up key parts of the nation's infrastructure.
The latest revelation is an example of how the U.S. government is attempting to take the lead in establishing cyber-warfare doctrines that include coordinating security measures with universities and strategically important industries -- especially the energy and transportation industries -- to thwart potentially harmful attacks by foreign governments or terrorists.
Between December 2011 and June 2012, hackers targeted 23 natural gas companies, which led to the theft of potentially sensitive information that could be used to take control of the networks that keep gas flowing safely, according to a confidential government report obtained by the Christian Science Monitor.
The report stops short of blaming the Chinese military for the cyber-intrusions, but security experts claim the signatures of the malicious computer code used to obtain the information suggest that a shadowy Chinese government-linked espionage group is to blame.
The military calls this type of threat the “kinetic effect” of cyber warfare, which goes beyond the theft of, say, credit card information or sensitive classified government intelligence. The “kinetic effect” is about taking physical control of an environment: railroad switches, refinery safety valves, power grids or, in this case, whatever keeps natural gas compressors from overloading and exploding.
“Anyone can blow up a gas pipeline with dynamite. But with this stolen information, if I wanted to blow up not one, but 1,000 compressor stations, I could,” Wlliam Rush, a retired energy industry scientist who has worked to boost network security in the natural gas industry, told the Monitor. “I could put the attack vectors in place, let them sit there for years, and set them all off at the same time. I don’t have to worry about getting people physically in place to do the job, I just pull the trigger with one mouse click.”
While this may sound like the plot to the next Michael Bay action film, U.S. intelligence is taking it seriously.
A 2010 report from the U.S. Department of Homeland Security says the threat to so-called ICS, or Industrial Control Systems, is real.
“Penetration activities may render ICS components inoperable, alter system data, or even cause economic or physical damage by manipulating the physical system,” the report said.
The Pentagon’s Defense Advanced Research Projects Agency has spearheaded the effort to get academic institutions and companies to work together to prevent virtual and kinetic cyberattacks. It even has a Hollywood-friendly name: Plan X, a five-year, $110-million program, according to the Washington Post.
© Copyright IBTimes 2025. All rights reserved.