North Korean Cyberattacks More Sophisticated, Hackers Impersonating Scholars Now: Report
North Korean cyber attacks that target journalists who cover the country’s news and non-governmental organizations that deal with North Korean human rights have become more sophisticated, reports the Daily NK- an online newspaper with a focus on North Korean issues. The report appeared on their website on Nov 27.
As per the report, earlier, hackers used to send emails to random targets that would have attached files with malicious code. However, a new “targeted strike” strategy is apparently in vogue now.
With this strategy, the attackers use the phone number of the individual they wish to target and reach the person through a message on KakaoTalk — a popular messaging app used in South Korea.
The newspaper also published an image showing a hacking attempt made against a journalist using the KakaoTalk app on Nov 22.
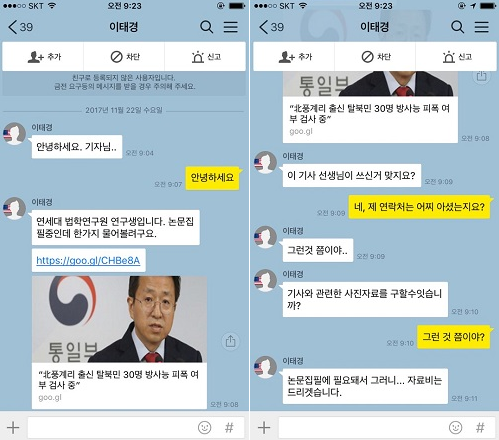
In this case, the attacker impersonated researcher Lee Tae Kyung from Yonsei University — a private research university located in Seoul. She sent a link to the journalist claiming that it contained Lee’s collected research papers. When the journalist — who didn’t have any connection with Lee — asked the sender how they got his phone number, the latter evaded the question.
The hacker also requested from the journalist a few images relevant to Lee’s research, with the promise of financial compensation for the pictures.
This request seemed odd to the journalist.
First of all, the journalist was unable to identify the image that was requested. Also, the thumbnail image that was used for the relevant article was a simple picture taken at a Unification Ministry briefing(The Unification Ministry is South Korea’s executive department that exists to promote Korean unification). Also, it was noticed that the hacker’s language was grammatically awkward, which suggested that he may not be from South Korea.
Seeing such oddities, the journalist sent the attached file that was shared with him by the hacker to a cybersecurity expert.
After performing an analysis on the file, it was found that the malicious code in the file was exactly the same code that was used in previous North Korean cyber attacks.
As the cybersecurity expert, who spoke to the Daily NK on condition of anonymity said, “The logical inference to draw here is that this recent hacking attempt was sent from North Korea. Recently, we’ve seen North Korean hackers sending malicious code to targets on their cellphones.”
“If the victim of the cyber attack were to open the link on their smartphone, it’s likely the malicious code would have spread. If they opened the PC version, it might not have resulted in any sort of attack at all,” he added.
A unique feature of the code that was found in the file was that it was programmed to self-delete in time. The analyst, who was unable to find the malicious code at first after he received the link eventually found it by investigating the link history.
The newest attack apparently differs from the ones in the past in two main ways.
In the past, attacks were carried out impersonating research institutes and public institutions and sending a malicious attachment via email. But here, the chosen medium is KakaoTalk.
Whereas a hacker’s email might easily be identified as fraudulent, the appearance of the hacker’s message in a messaging app like KakaoTalk might give it a legitimate appearance.
Also, in the past the emails would contain messages related to North Korea. But now, the hackers seem to reach out directly to a person and engage in direct conversation regarding a topic the receiver might be familiar with.
This apparently makes the victims lower their guard and revs up their curiosity.
As of now, it’s unclear who is behind the latest attack.
© Copyright IBTimes 2025. All rights reserved.




















