Hacking Team Spyware Leaked Onto GitHub, And It Looks Like It's Going To Stay There
Advanced spyware used by some of the world's most repressive governments suddenly went open source last weekend. A 400GB cache of internal files from Hacking Team, a contractor that sold "offensive technology to the worldwide law enforcement and intelligence communites," was uploaded to the Internet Sunday and included source code.
Of course, that source code -- for software that can be called a cyberweapon -- was soon uploaded to GitHub, the primary service programmers use to host code online.
Under the username "HackedTeam," GitHub is currently hosting code for 53 programs and scripts originating from the Hacking Team dump. The spy tools include exploits for popular programs like Adobe Flash as well as software for eavesdropping and intercepting passwords. Although Hacking Team's spyware could cause real damage in the wrong hands -- it's allegedly been used to unmask journalists and activists around the world -- since it's already out in public, it will be extremely difficult to erase it from the Internet.
"I made the GitHub pages because I'm interested in keeping the source code, exploits and Hacking Team's actions as visible as possible. The goal is to facilitate the work of people looking to investigate or simply share the information," wrote the anonymous uploader in an email.
However, the GitHub page for HackedTeam was not available Tuesday morning and visitors were greeted with a note that said the page could not be found. GitHub did not decide to take the code down on purpose, confirming the pages were mistakenly hidden for a few hours by a spam-detection service. By Wednesday, the code was back online.
In a statement provided to International Business Times, a GitHub spokesperson said that the company doesn't "actively moderate the content that people share on GitHub, but when we receive reports of content that may be in violation of our Terms of Service, a diverse team investigates the content and surrounding facts thoroughly and responds as appropriate."
"GitHub had temporarily suspended my account with this notice: 'One of our mostly harmless robots seems to think you are not a human,'" the anonymous poster wrote, adding the page was put back up after he contacted support.
The HackedTeam page doesn't appear to violate any of GitHub's terms of service, although there is an item that says "you may not use the service for any illegal or unauthorized purpose." Although the Hacking Team software can be used for illegal purposes, disseminating the source code for study shouldn't be illegal. Hacking Team might have violated international law by selling its software to repressive regimes, but its code theoretically is protected free speech.
Hacking Team could potentially request to have its code taken off GitHub by filing a Digital Millenium Copyright Act takedown request since its code presumably is copyrighted. Companies like Sony and Microsoft have used DMCA to get private code off GitHub in the past. GitHub, however, publishes all DMCA takedown notices it receives, and it does not appear Hacking Team has made a request yet. A Hacking Team spokesperson confirmed to Vice Motherboard Tuesday the 400 GB dump is legitimate.
Hacking Team did not immediately respond to a request for comment although in a statement released Wednesday the company said:
Terrorists, extortionists and others can deploy this technology at will if they have the technical ability to do so. We believe this is an extremely dangerous situation. HackingTeam is evaluating if it is possible to mitigate the danger.
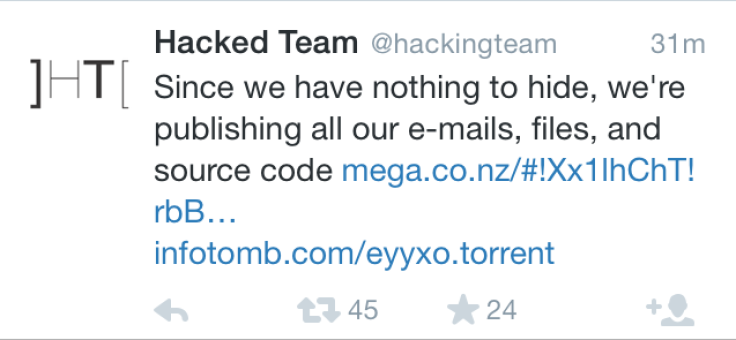
Whoever exploited Hacking Team also took over the company's Twitter account, and made several jokes about open sourcing its code, which is effectively what's happened. The Hacking Team data dump released tools for compromising Android phones, Windows desktops, and other computers into the wild in a way that both benevolent and malevolent hackers can continue to improve on them.
As of Wednesday, the HackedTeam account on GitHub had 1,400 followers and certain programs had been "forked," or copied by programmers intending to improve on them, more than 100 times.
© Copyright IBTimes 2024. All rights reserved.












