Snowden Says FBI’s Claim That Only Apple Can Unlock iPhone Is ‘Bulls--t’
Edward Snowden says the FBI’s claim that only Apple is capable of unlocking the iPhone used by one of the San Bernardino, California, shooters — which is at the center of the privacy and encryption debate that has put Washington and Silicon Valley on a collision course — is “bulls--t.”
Speaking as part of a panel at Common Cause’s Blueprint for Democracy conference in Washington Tuesday, Snowden said: “The FBI says Apple has the ‘exclusive technical means’ to get at this phone. Respectfully, that’s bulls--t.”
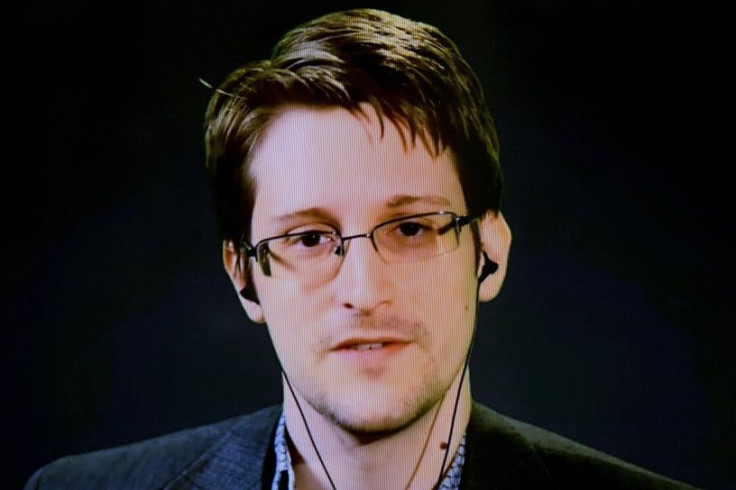
Snowden was speaking via video link from Russia where he has been living since he fled the United States in the summer of 2013 before releasing a huge cache of top secret documents he stole while working as a contractor for the National Security Agency.
To back up his claims, Snowden tweeted a link to an article published by the American Civil Liberties Union (ACLU) this week, which explains in detail how the FBI could unlock the iPhone without Apple’s help. The FBI’s court order first demands that Apple disable a security feature that would erase all data on the phone if the wrong PIN code is entered 10 times.
Daniel Kahn Gillmor, technology fellow at the ACLU, says this aspect of the FBI’s order is fraudulent. “The truth is that even if this feature is enabled on the device in question, the FBI doesn’t need to worry about it, because they can already bypass it by backing up part of the phone (called the 'Effaceable Storage') before attempting to guess the passcode.”
Gillmor says that when Apple auto-erases the iPhone after 10 failed PIN code attempts, it does not actually delete all the content (which would take several minutes) but it deletes the “file system key” that is stored in a part of the iPhone’s flash memory known as “Effaceable Storage” making it easy to delete quickly.
The FBI could, Gillmor says, simply copy the entire flash memory from the iPhone (which would include the file system key) before it tries 10 passcode attempts. It can then re-try indefinitely, because it can restore the flash memory from its backup copy.
To do this, the FBI would need to disconnect the memory chip from the iPhone’s circuit board and use a device that could read such chips to copy all the data stored on it. In order to save time, Gillmor says the FBI can put a “test socket” on the circuit board to speed up the process of repeatedly testing PIN codes.
Gillmor says the FBI is simply ignoring this possibility because it wants to make a point. “The FBI wants us to think that this case is about a single phone, used by a terrorist. But it’s a power grab: law enforcement has dozens of other cases where they would love to be able to compel software and hardware providers to build, provide, and vouch for deliberately weakened code,” he said.
This is the latest suggestion of how the FBI could unlock the iPhone without Apple's help which have previously included a process known as “decapping,” where an engineer would physically take out the phone’s memory chip and use a combination of acid and a tiny laser drill to extract bits of data. While many experts have claimed the FBI has the ability to unlock the iPhone on its own, others disagree.
“There’s nothing that anybody can do — there’s no technology, and there’s no secret trick, that anybody’s developed yet that would bypass these security measures,” Yaniv Schiff, director of digital forensics at Forensicon, a Chicago-based consulting firm told International Business Times. “There are vendors that offer password-cracking methods, but only for previous releases of the iOS platform.”
© Copyright IBTimes 2024. All rights reserved.












