Spying Program Leaked By Snowden Is Tied To Campaign In Many Countries
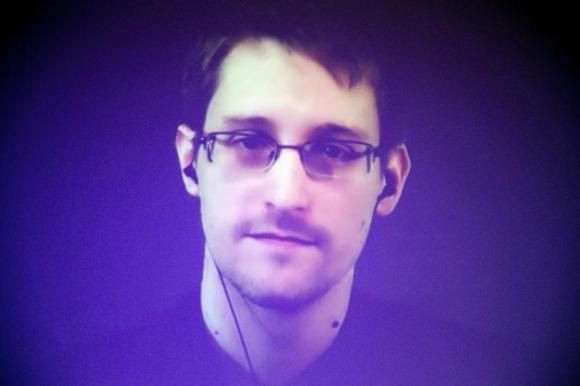
(Reuters) - A program used by U.S. and British spies to record computer keystrokes was part of sophisticated hacking operations in more than a dozen countries, security experts said on Tuesday, after former NSA contractor Edward Snowden reportedly leaked the source code for the program.
On Tuesday, researchers at security software firm Kaspersky Lab said that much of that code, published this month by German magazine Spiegel, matched what they previously found in machines infected by Regin, a major suite of spying tools exposed in November.
Lead Kaspersky researcher Costin Raiu said that the keylogging program, called Qwerty, would work only with Regin, and that it appeared several Western countries' spies had been using Regin over the course of a decade.
"Multiple attacker groups are using the Regin platform, which is a new conclusion for us,” Raiu told Reuters.
Spiegel and other publications reported earlier that Regin had been used in the hacking of Belgian telecommunications provider Belgacom, which slides provided by Snowden said was targeted to enable spying on mobile phones in Europe.
Overall, the malicious software has been discovered at more than two dozen sites in 14 countries, including Russia, India, Germany and Brazil. Targets included government agencies, financial institutions and multilateral bodies.
The NSA did not respond to a request for comment. After past Snowden disclosures, it has avoided discussing specific operations but said it complies with U.S. law, which allows broad surveillance overseas.
The new findings suggest that Regin was a platform for spying operations that was shared among the so-called Five Eyes—the United States, United Kingdom, Canada Australia, and New Zealand.
In its own November report on Regin, top U.S. antivirus company Symantec Corp said it was extraordinarily well disguised, and that even when traces were found it was difficult to know the purpose. Like some other top-tier spying programs, Regin has different modules that can be installed to achieve different ends.
Symantec said it found victims in the telecom industry as well as energy, airline and research concerns.
© Copyright Thomson Reuters {{Year}}. All rights reserved.





















