Cryptowall 4 Is In The Wild, After Previous Versions Extorted $325 Million From Ransomware Victims
The world's most dangerous ransomware just got even scarier. A fourth version of Cryptowall, the ransomware strain that has befuddled the world's top cybersecurity experts, has been spotted in the wild, now with more sophisticated encryption and disguising tactics.
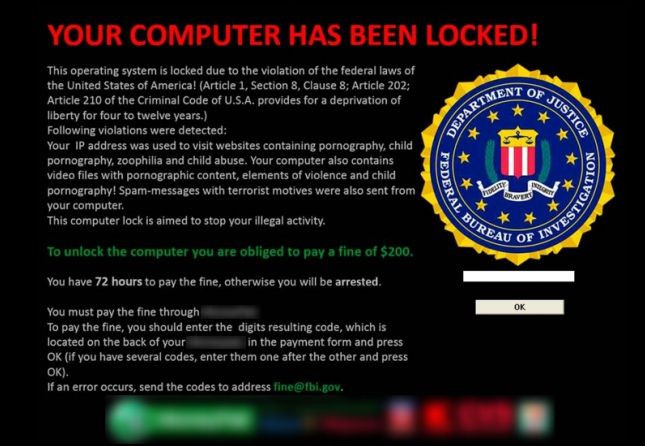
Ransomware is a type of malicious software that encrypts the data on a target machine and holds it hostage until the victim pays a bitcoin ransom, often in the thousands of dollars. The FBI said it received 992 Cryptowall complaints in 2014, with victims paying more than $18 million, and small businesses are increasingly under threat. The real number is likely closer to $325 million, and it's probably all thanks to a single group, according to the Cyber Threat Alliance.
Now the group responsible is targeting Linux website designers and injecting malware onto servers that host multiple machines, cybersecurity journalist Brian Krebs reported Monday. It now changes filenames and file contents, as well, meaning it's more difficult for victims to find out how much of their computer has been taken over. That's not to mention a threat last week that promised to publish victims' data online if they didn't pay up.
“Cryptowall 4.0 still includes advanced malware dropper mechanisms to avoid antivirus detection, but this new version possessess vastly improved communication capabilities,” wrote Andra Zaharia of Heimdal Security. “It includes a modified protocol that enables it to avoid being detected, even by second-generation enterprise firewall solutions. This lowers detection rates significantly compared to the already successful Cryptowall 3.0 attacks.”
Not that it was necessary. An FBI investigator admitted last month the bureau already has no choice but to recommend ransomware victims just pay the fee.
© Copyright IBTimes 2025. All rights reserved.



















