How To Protect Against Meltdown And Spectre: Patches For Windows, MacOS, Android
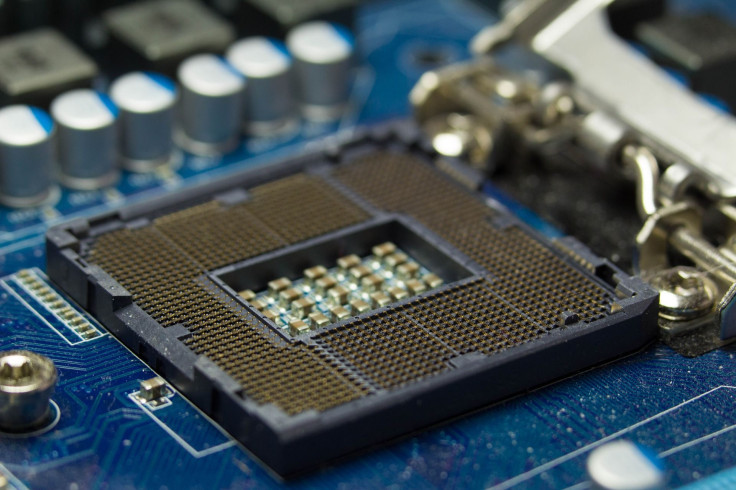
On Wednesday, security researchers disclosed two major security flaws discovered in computer processors that could impact just about every machine—from desktop computers to smartphones—released in the last two decades.
The bugs—discovered by researchers from Google's Project Zero, Graz University of Technology, the University of Pennsylvania, the University of Adelaide in Australia, and security companies Cyberus and Rambus—allow apps and processes to gain access to highly privileged and sensitive information.
The first of the bugs is called Meltdown, named for how the exploit allows attackers to “melt” the security boundaries that are typically in place. When executed, Meltdown allows an attacker to break the mechanisms that prevent standard applications from accessing system memory. Meltdown affects just about every Intel processor produced since 1995.
Other processor makers including AMD and ARM thus far have not been plagued by Meltdown, but are affected by a similar bug called Spectre. The flaw tricks applications into providing information about the machine. Just about every machine using a modern processor is at risk from Spectre, including desktops, laptops, smartphones and cloud servers.
While Meltdown grabbed the initial headlines—much to the chagrin of Intel—the researchers who discovered the bugs warn that Spectre “is not easy to fix” and “will haunt us for quite some time.”
The security flaws should not be taken lightly. It’s unknown if either Meltdown or Spectre have been executed in the wild—the United States Computer Emergency Readiness Team reported that it is not aware of any such attacks—but a proof-of-concept attack carried out by researchers revealed the bugs could be exploited to steal passwords and other sensitive data stored on a system.
Luckily, it is possible to protect against Meltdown and Spectre. Patches have already been made available by a number of vendors and fixes will continue to come out in the coming days and weeks. It’s up to users to install the patches in order to ensure that their machines are secure.
Here are the fixes that you can install right now in order to protect your devices:
Web Browsers
It’s not just computers that are at risk from these attacks—web browsers are vulnerable as well. Most of the popular browsers have already taken steps to issue a fix to mitigate the possibility of “timing attacks” like Meltdown and Spectre.
Firefox version 57 , first released in November 2017, includes protection against such attacks.
A security patch issued by Microsoft on January 3 adds new protections to its Internet Explorer and Edge browser.
Google will have a fix live in its browser with the release of Chrome 64 . The update is slated to be available on January 23.
Android
Google has a security update set to be released on January 5. For devices made by Google, the update should be downloaded and installed automatically. For devices from other manufacturers, the process can be a bit slower. Regardless of the device maker, users should check to see if the update is available by following these steps:
Open the device's Settings app
Near the bottom, tap “System,” then “About phone” or “About tablet.”
Scroll down to "Android version" and "Android security patch level."
Make sure the patch level is updated to Android 2018-01-05 .
If the patch level is not up to date, do the following:
Open the device’s Settings app.
Near the bottom, tap “System” then “System update.”
If an update is available, download and install it.
iOS
Apple has been mum on the issue of Spectre and Meltdown since the bugs were revealed and has not made it clear yet if any of its processors are affected. iOS devices including iPhones and iPads use processors from ARM—though starting with the iPhone 5s, Apple began building its own, custom chips.
ARM has issued a statement that it believes the majority of its processors are not affected by Meltdown or Spectre. Until Apple provides more details, it’s difficult to know if its mobile devices are at risk from the flaws. It should go without saying, but keeping devices up to date is the best way to protect against attacks, so checking for the most recent update for iOS should be the first step.
To check for an iOS update, do the following:
Open the Settings app
Tap the General menu and tap “Software update”
If an update is available, download and install it
Windows
Microsoft released a security update Wednesday that will help mitigate the threat posed by Meltdown and Spectre. The update, available for Windows 10, is identified as KB4056892 (OS Build 16299.192).
Windows 10 machines should automatically download and install the update. Though it is possible to delay such automatic updates, it’s best to let this one install, which will likely require a full restart.
The update can also be downloaded from Microsoft’s update catalog if the update has not yet been made available through the Windows Update tool.
Intel has also published a tool that can check a machine’s firmware (the software embedded in a piece of hardware that tells it how to operate). The Intel-SA-00086 Detection Tool is available for machines running Windows 10, 8.1 and 7 and can determine if a PC requires a firmware update.
MacOS
Mac users who have been keeping up with security updates should already be protected from Spectre and Meltdown; Apple began mitigating the attack with the release of macOS High Sierra 10.13.2 , first made available December 6, 2017.
Alex Ionescu, the Vice President of EDR Strategy at security firm CrowdStrike, wrote on Twitter that MacOS 10.13.3 will have “some surprises” that will also help to defend against the threats posed by the security flaws.
To make sure a Mac is up to date, open the App Store and click on the “Updates” tab. If an update is available, it should appear. Download and install the update—and note that the process may require the machine to restart.
© Copyright IBTimes 2025. All rights reserved.




















