Popcorn Time Hacker Finds A Way To Spread Malware Via Movie Torrent Software
With more popularity comes the need for better online security. Popcorn Time found that out when a cybersecurity researcher injected malicious code into the piracy software, potentially putting thousands of users at risk.
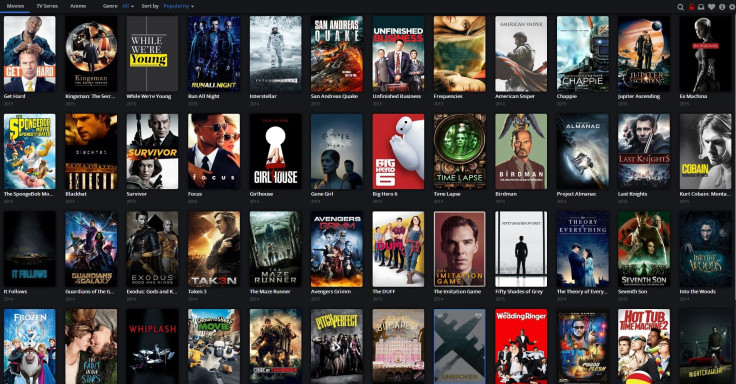
Antionios Chariton, a Greek cybersecurity researcher, told TorrentFreak he discovered a number of serious flaws in PopcornTime.io, perhaps the most popular version of the piracy software. Popcorn Time is a loosely affiliated networks of sites that makes it possible for users to download movie torrents directly to their computer via a bright, clean interface that looks more like a legitimate streamer than the virus-infused Pirate Bay.
Or so it seemed, until Chariton maniupulated Popcorn Time's software by exploiting its HTTP and NodeJS protocol to crearte an XSS security vulnerability.
“This essentially is Remote Code Execution on the computer that runs Popcorn Time,” Chariton told TorrentFreak. “We injected malicious JavaScript and the client application executed the code. Using this attack we can show fake maessages or even do something smarter. Since the application is written in NodeJS, if you find an XSS vulnerability, you are able to control the entire application.”
It's not clear how many, if any, other Popcorn Time versions include the vulnerability.
“This attack requires that the attacker is either inside the local network, inside the host machine, or has poisoned the [Domain Name System] servers,” Popcorn Time administrators told TorrentFreak. “In any case, there are far more valuable attacks than simply hitting Popcorn Time. Especially because it does not run with elevated priveleges and won't let the attacker install new programs, for example.”
© Copyright IBTimes 2025. All rights reserved.




















