Chinese Hackers Continue To Target US Firms Despite Cybersecurity Agreement

Hackers linked to China attempted to violate a cybersecurity agreement between Washington and Beijing just a day after the leaders of the two nations announced the deal, according to a newly published analysis by an American cybersecurity firm.
CrowdStrike Inc. -- a company with close ties to the U.S. government -- also claimed that in the three weeks since the deal was finalized, U.S. companies continued to face repeated, albeit unsuccessful, intrusions from China-linked hackers.
“We assess with a high degree of confidence that these intrusions were undertaken by a variety of different Chinese actors, including Deep Panda, which CrowdStrike has tracked for many years breaking into national-security targets of strategic importance to China, as well as commercial industries such as Agriculture, Chemical, Financial, Healthcare, Insurance, Legal, Technology and many others,” the company said, in its report released Monday.
Deep Panda has earlier been linked to the Chinese military, and is believed to have been behind the attack on U.S. health insurance company Anthem Inc., which took place earlier this year.
Chinese attempts at cyberespionage against the U.S. have been a key sticking point between the two nations.
Last month, just days before Chinese President Xi Jinping was scheduled to meet U.S. President Barack Obama, U.S. National Security Advisor Susan Rice warned that China’s activities in cyberspace were putting an “enormous strain” on bilateral ties.
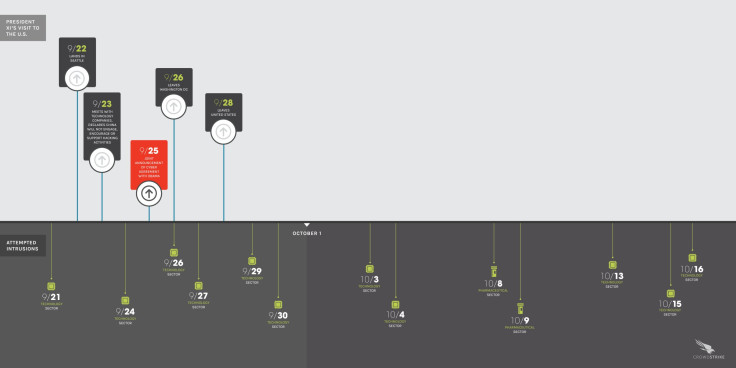
On Sept. 25, Obama and Xi announced a new agreement banning the hacking of private firms by entities linked to either country for economic gain.
However, according to the timeline of the China-linked intrusions released by CrowdStrike, “commercial entities that fit squarely within the hacking prohibitions covered under the Cyber agreement” are still being targeted.
“The intrusion attempts are continuing to this day, with many of the China-affiliated actors persistently attempting to regain access to victim networks even in the face of repeated failures,” the company, which employs former FBI and NSA cyberexperts, said, in its report. However, it did not name the companies that were targeted.
© Copyright IBTimes 2025. All rights reserved.




















