A Simple Text Message Can Put iPhone Users At Risk, Project Zero Reports
A simple text message could offer a path for hackers to break into an iPhone user’s privacy.
Natalie Silvanovich, a Google Project Zero researcher, unveiled a presentation Wednesday on how hackers will be able to break into iPhone users’ data through a simple text message. The presentation was done in a Black Hat security conference held in Las Vegas.
Silvanovich revealed that Apple’s iMessage has what is called “interaction less” bugs. The said bugs could be a platform for hackers to not just access but even control the user’s device once exploited.
The Project Zero researcher further stated that Apple is in the process of patching the said bugs. She also revealed that the Cupertino tech giant successfully patched six vulnerabilities as of the moment and will continue to do more.
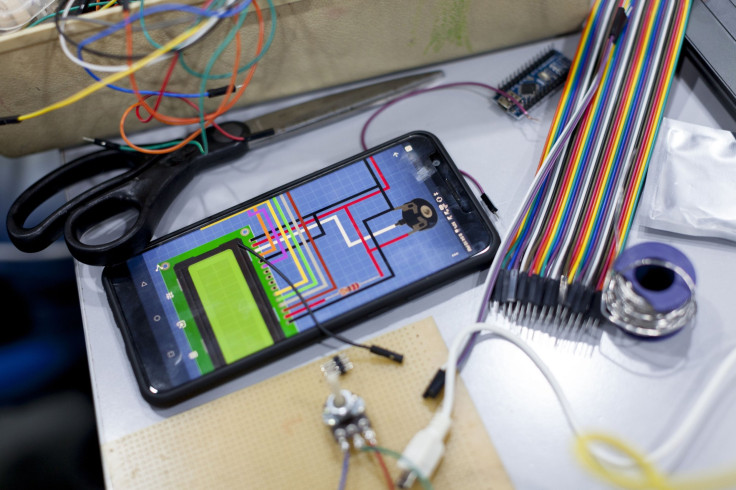
Silvanovich worked together with Samuel Groß, a Project Zero member, and used reverse engineering to unveil a number of the above-mentioned vulnerabilities. This discovery changed the assumption they had over iMessage’s immunity against exploits as it has always been known to have a lockdown target not to mention it's been highly scrutinized.
The “interaction less” bugs that pose a serious risk to iPhone users through a simple text message work through the server. The vulnerability opens up without the iPhone user even having to open the iMessage.
It works like this. The hacker sends a message to the iPhone user through the iMessage. The server will then send back the specially crafted message to the sender duplicating the Apple customer’s SMS message or image format.
The Project Zero researcher describes the bug as one that is relatively difficult to fix. She further added that there is a lot of additional attack surface and that not all of them can found in the software. She also reminded the iPhone users that every library that they use can become an attack surface.
Groß and Silbvanovich’ quest to find and patch the “interaction less” bug ignited when a WhatsApp vulnerability surfaced over news. The bug was so aggressive that hackers were able to access a phone by calling even if the user did not answer the call.
© Copyright IBTimes 2025. All rights reserved.




















