Flame: World?s Most Complicated Cyber Espionage Malware Discovered On Thousands Of Computers In Middle East
Researchers at the Russian security firm Karpersky have discovered a new highly sophisticated malicious program that has been used as a cyber weapon to collect private data from thousands of computers in Middle East countries like Iran and Israel and also in North Africa. The complexity and functionality of the new malware made it one of the most complex threats ever discovered, according to researchers.
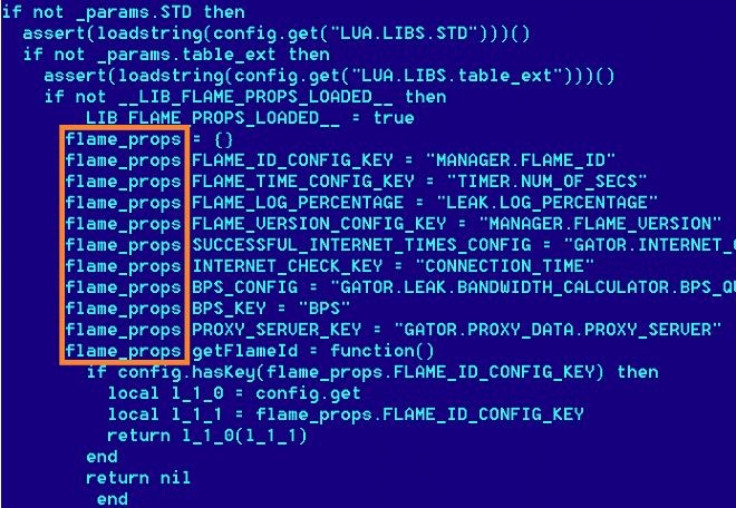
Codenamed Worm.Win32.Flame, the malware was discovered by Kaspersky Lab's experts during an investigation prompted by the International Telecommunication Union (ITU). Flame was designed to perform cyber espionage and is capable of stealing valuable information, including computer display contents, information about targeted systems, stored files, contact data and even audio conversations.
The 'Flame' cyber espionage worm came to the attention of our experts at Kaspersky Lab after the UN's International Telecommunication Union came to us for help in finding an unknown piece of malware which was deleting sensitive information across the Middle East, Kaspersky Lab Expert Alexander Gostev wrote in a blog post.
While searching for that code - nicknamed Wiper - we discovered a new malware codenamed Worm.Win32.Flame.
Kaspersky Lab has told BBC News that Flame is believed to be operating since August 2010, with active development going on till date. The security firm believed the attack was state-sponsored. However, Kaspersky was not sure of its exact origin.
According to researchers, the creators of Flame changed the dates of creation of the files to mislead investigators. The files are dated 1992, 1994, 1995 and so on, but all of them have been clarified as false dates.
Different From Duqu And Stuxnet
Although the features of Flame have very little to share with earlier notorious cyber weapons like Duqu and Stuxnet, what put it in the same category of super cyber weapons are the geography of attacks, use of specific software vulnerabilities, and the fact that only selected computers are being targeted.
Stuxnet and Duqu belonged to a single chain of attacks, which raised cyberwar-related concerns worldwide. The Flame malware looks to be another phase in this war, and it's important to understand that such cyber weapons can easily be used against any country. Unlike with conventional warfare, the more developed countries are actually the most vulnerable in this case, said Eugene Kaspersky, CEO and co-founder of Kaspersky Lab.
Once getting the access to a computer, Flame steals information from it and then sends it to a network of command-and-control servers located in many different parts of the world. The stolen information can include documents, screenshots, audio recordings via microphones and interception of network traffic, making Flame one of the most advanced and complete attack-toolkits ever discovered.
Flame has the ability to replicate over a local network using several methods, including the same printer vulnerability and USB infection method exploited by Stuxnet, according to Kaspersky Lab's reports.
The Verge has reported that it's confirmed that the worm has spread over local area networks to fully-patched Windows 7 systems. Interestingly, Flame surveys a system and can uninstall itself from machines it thinks are not of its use.
The report added that the malware itself can be up to as large as 20MB, which is about 20 times larger than Stuxnet. While most malware is as simple and small as possible, making it easy to hide the malicious code and instill it onto unsuspecting machines, Flames massive size made it hard to identify since no one was looking for it. Additionally, Flame consists of many different plug-ins - up to 20 - which have different specific roles.
A Government-Backed Cyber Weapon?
According to Kaspersky's chief malware expert Vitaly Kamluk, the size and sophistication of Flame suggested it was not the work of independent cybercriminals, but more likely to be government-backed.
Currently there are three known classes of players who develop malware and spyware: hacktivists, cybercriminals and nation states, BBC News quoted Kamluk as saying. Flame is not designed to steal money from bank accounts. It is also different from rather simple hack tools and malware used by the hacktivists. So by excluding cybercriminals and hacktivists, we come to conclusion that it most likely belongs to the third group.
The countries that have been targeted by Flame malware include Iran, Israel, Sudan, Syria, Lebanon, Saudi Arabia and Egypt.
The geography of the targets and also the complexity of the threat leave no doubt about it being a nation-state that sponsored the research that went into it, Kamluk said.
According to Kaspersky, ITU will use the ITU-IMPACT network, consisting of 142 countries and several industry players, to alert governments and the technical community about this cyber threat, and to expedite the technical analysis.
© Copyright IBTimes 2024. All rights reserved.












