ISIS Hackers Love To Threaten The US, But Don't Expect Them To Turn Off the Lights Quite Yet
The Islamic State group wants the world to believe it’s not just a terrorist group but a dangerous hacking collective capable of infiltrating critical digital networks in the U.S. and elsewhere. Don’t believe the hype, at least not yet.
Hackers who claim to be affiliated with the extremist group -- also known as ISIS, ISIL and Daesh -- have a “strong intent” to penetrate the U.S. energy grid, U.S. officials told CNN in October. But the group has shown no indication it’s capable of such an attack, and national security officials have consistently warned that rival nation-states pose the biggest threat to the 16 critical infrastructure sectors in the U.S.
Still, ISIS supporters have sought to portray them as a credible hacking threat over the past six months by claiming to “leak” information about U.S. government and military personnel -- which was actually already available.
“Basically, there’s a slew of hacking collectives who support ISIS, but thus far there’s not a group that’s officially hacking on their behalf,” said Alex Kassirer, an ISIS hacking analyst at the global intelligence firm Flashpoint. “They’ve been extremely prolific in terms of how much they’ve been doing, but some of the data dumps they’ve done are actually recycled from groups like Anonymous and Lulzsec.”
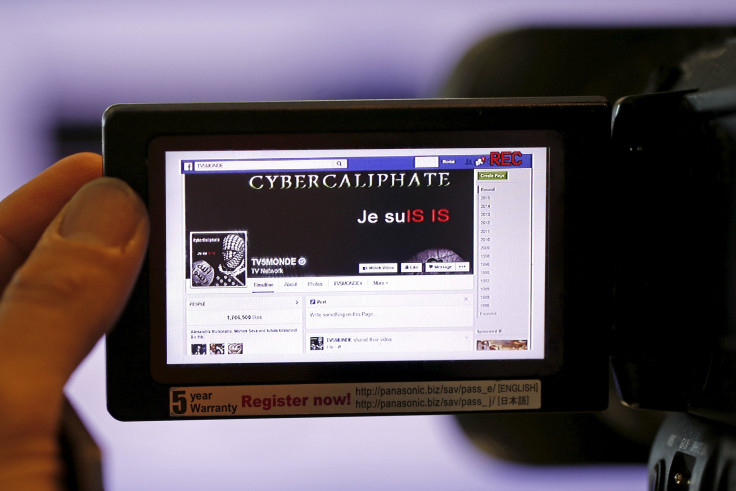
Various groups – Rabitat al-Ansar, the Islamic State Hacking Division, the Islamic State Cyber Army, among others – have claimed to hack into U.S. federal computer networks and threaten hundreds of employees listed there by publishing photos and identifiable information (all of which is believed to have been available already). Another group, the Cyber Caliphate, has hacked U.S. military Twitter feeds, including one belonging to U.S. Central Command.
That hack, a relatively low-level spearphishing attack, was attributed to Junaid Hussain, a 21-year-old hacker who rose to become one of ISIS’ most influential propagandists, who tricked an employee into revealing a password. Hussain (also known as Abu Hussain al-Britani) took credit for defacing a number of French websites and U.S. media sites and for releasing the personal address of U.S. blogger Pamela Geller along with the message “Go Forth.” Hussain was reportedly killed in August by a U.S. drone strike, proof that he warranted enough attention from the military to warrant an airstrike.
“A lot of this is fearmongering and puffing out their chest, but there is credibility there,” Kassirer said.
One fear is that ISIS -- which funds its terrorist activity through oil sales, crime and donations from powerful officials throughout the Middle East – will either recognize one group of aspiring hackers or simply hire their own. There’s no indication they’ve done so yet, though, and Kassirer called any attempt to project such a decision “pure speculation.”
It would likely take a state-sponsored hack to infiltrate most critical infrastructure in the U.S., ranging from the energy sector, financial services, public health and the defense industry. The American electrical grid, for example, is actually a mishmash of smaller grids that don’t operate on a single switch. It would take an advanced, highly technical group of agents working in unison to put a large number of Americans in the dark.
That could change soon, as more facilities transfer to autonomous systems. Instead of an engineer having to authorize a command by pressing a button, for instance, machines will communicate directly with one another and may not notice when software vulnerability is being exploited.
“For a lot of these extremist groups, the cyber angle is absolutely something they’re exploring,” said Jasper Graham, U.S. chief technology officer at the cybersecurity firm Darktrace, who spent 12 years in the National Security Agency. He added that something as simple as a spearphishing attack could enable an inexperienced hacker to access machines they don’t even understand.
“They can do something as simple as ‘I don’t know what these controls do, but I’m going to put them all on max’ or turn off a safety feature, [and it may have] catastrophic consequences,” Graham said. “If you’re ISIS and your endgame is destruction and terror, then you don’t care what happens.”
© Copyright IBTimes 2025. All rights reserved.



















