MEGA Chrome Extension Hacked To Steal Monero Cryptocurrency
UPDATE: 4:30 a.m. EDT — MEGA responded to the hack of its Chrome extension and expressed dissatisfaction with Google's Chrome Web Store security measures.
In a blog post, MEGA said it updated the extension with a clean version (3.39.5) four hours after the breach occurred, while Google removed the older version of the extension from the Chrome Web Store five hours after the breach. The one-hour time gap, MEGA believes, helped attackers pull off the extension hijack.
"We would like to apologize for this significant incident. MEGA uses strict release procedures with multi-party code review, robust build workflow and cryptographic signatures where possible. Unfortunately, Google decided to disallow publisher signatures on Chrome extensions and is now relying solely on signing them automatically after upload to the Chrome webstore, which removes an important barrier to external compromise," MEGA said.
The file-sharing host also confirmed users of the extension would have been affected if it was installed at the time of the incident, with "auto update enabled and you accepted the additional permission, or if you freshly installed version 3.39.4. Please note that if you visited any site or made use of another extension that sends plain-text credentials through POST requests, either by direct form submission or through a background XMLHttpRequest process (MEGA is not one of them) while the trojaned extension was active, consider that your credentials were compromised on these sites and/or applications."
Further, META said it was investigating the exact nature of the compromise.
Original story:
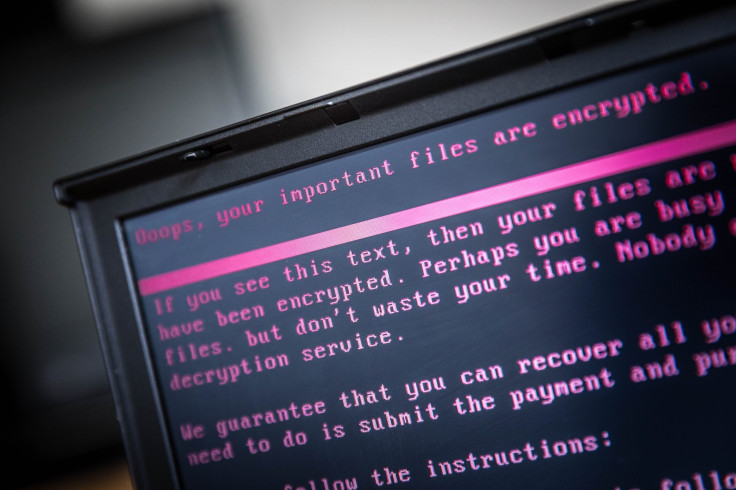
The latest version of the MEGA extension for Google’s Chrome browser has been hacked to include functionality that allows the hackers to steal cryptocurrency in addition to other sensitive information. According to several recent posts on Twitter and Reddit, MEGA version 3.39.4 has been compromised.
"If you use the official MEGA Chrome extension, please stop using it immediately" a Reddit user said . "It includes functionality to collect login usernames and passwords for many common websites, including but not limited to: Google, Facebook, MyEtherWallet, MyMonero, GitHub, Microsoft Live/one drive."
SerHack, developer of the Monero cryptocurrency, tweeted warnings that urged users to remove the extension after a review of the code revealed several cryptocurrency wallets were affected.
!!! WARNING !!!!!!! PLEASE PAY ATTENTION!!
— SerHack (@serhack_) September 4, 2018
LATEST VERSION OF MEGA CHROME EXTENSION WAS HACKED.
Version: 3.39.4
It catches your username and password from Amazon, GitHub, Google, Microsoft portals!! It could catch #mega #extension #hacked@x0rz pic.twitter.com/TnPalqj1cz
MyEtherWallet (an open-source, client-side interface for generating Ethereum wallets & more) also warned users to uninstall the MEGA Chrome extension following reports of the hack.
** MEWS ALERT **
— MyEtherWallet | MEW (@myetherwallet) September 4, 2018
We're getting reports that the latest version of the MEGA Chrome Extension was hacked.
We suggest you uninstall it immediately, for your own safety! 👆🏾🧐 https://t.co/Z5Kh7aDSXd
The extension — it claims to improve browser performance by reducing page loading times, and also provides a secure cloud storage service — has been removed from the Chrome Web Store. Clicking the link for the extension resulted in a 404 error.
There were a number of ongoing discussions on Reddit about the hack and users blamed the lack of supervision from Google Chrome in verifying the source code (a text listing of commands to be compiled or assembled into an executable computer program) of extensions.
"I do some extension development. Google doesn't check your code when they put it on the webstore. They just do automated tests on your code an [sic] publish it within a few hours," a developer on Reddit commented. "Mozilla has humans that check your code for security and quality. Which can take a very long time (days to weeks). Due to this, Firefox is less prone to these types of attacks."
This isn’t the first time the Chrome store hosted a phishing extension centered on private keys. A few months ago, MetaMask, an Ethereum wallet that also serves as a bridge between web browsers and the ethereum blockchain, was delisted from the Chrome Web Store. This was announced by the MetaMask team on their Twitter page and the extension was restored to the store around five hours later. When the original MetaMask was removed, an employee at Ethereum startup and incubator ConsenSys wrote in his blog, "What was left when one searched the term 'MetaMask' on the store was a few re-branded MetaMask forks and one ambiguously branded lookalike." This situation created the risk of phishing, in which attackers would trick would-be users into downloading fake files containing malware.
It was unclear whether the changes to the MEGA extension are the result of a hack of the team’s Chrome Web Store account, or whether there was a different security issue. The last commit to the team’s GitHub was made 4 months ago, and the update that went out recently wasn’t included in the list.
The update to the MEGA extension prompted the add-on to apparently ask users for permission to read data on all websites. This red flag caused some users to criticize or uninstall the add-on.
"There was an update to the extension and Chrome asked for new permission (read data on all websites). That made me suspicious and I checked the extension code locally (which is mostly javascript anyways). MEGA also has the source code of the extension on github." Ganother Reddit user explained. "There was no commit recently. To me, it looks either their Google Webstore account was hacked or someone inside MEGA did this. pure speculation though."
MEGA had not responded to the news of the security breach of its extension at the time of writing. Monero (XMR) did not seem to be affected much by the hack. Instead, it saw a rise of 2.06 percent in the last 24 hours with the price of $138.46, as tracked by CoinMarketCap.
© Copyright IBTimes 2025. All rights reserved.




















