CryptoLocker Virus: Hackers Offer 'Second Chance' To Recover Files At Five Times Original Ransom

Did you catch the CryptoLocker malware and refuse to pay the ransom to get your files back? It appears now that the hackers responsible for the virus are giving users infected with CryptoLocker a second chance, but for five times the cost of the original ransom.
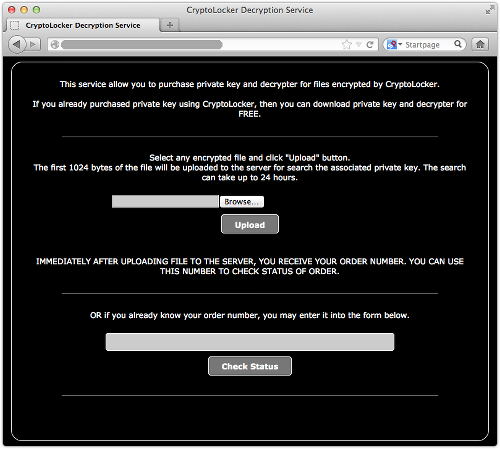
The CryptoLocker hackers have set up an online decryption service that will allow users access to their files even after the initial time limit expired. Instead of $300, the original ransom, this service costs 10 Bitcoins. That’s about $2,400 using the current exchange rate on Mt. Gox, and the process will take about 24 hours to complete.
“We're guessing that the delay is because the crooks have to run a brute force attack against themselves,” Paul Ducklin said on the Naked Security blog of security firm Sophos.
CryptoLocker disguises itself as a FedEx or UPS tracking notification and has also appeared in phony emails claiming to be from legitimate businesses. Once the link is opened, CryptoLocker scans the computer’s hard drive for documents, spreadsheets, photos, AutoCAD design files and Adobe Photoshop projects. It encrypts these files and launches a pop-up window with a 100-hour countdown and details on how to pay the $300 ransom. Some users have reported a countdown of only 72 hours.
If the ransom is paid, the hackers deliver a decryption key for the user to access their files again. If not, the key is destroyed and the user may forever lose access to his or her files.
It’s extortion, plain and simple, but security experts say that there is very little a user can do once the decryption key is destroyed. The only fix would be to regularly back up data on a separate hard drive, wipe the infected computer and restore the files from the backup. Of course, these users run the risk of the CryptoLocker virus making its way to the backup.
The new decryption service could be useful for users that found the CryptoLocker malware and deleted it after it encrypted the files, making it impossible to purchase the decryption key.
Still, security experts still advise users to not given in to the hackers’ demands. A helpful article from Sophos explains how the CryptoLocker malware works and how to prevent it from infecting your computer.
© Copyright IBTimes 2025. All rights reserved.






















