HR is transforming into a strategic, data-driven powerhouse central to organizational success. At the forefront of this movement is Sarala Nishank Pathi.
In the high-stakes world of specialty retail, where trends are ephemeral and customer loyalty is hard-won, the gap between a brand's digital promise and its operational reality can be a chasm. Bridging this chasm is not just a technical challenge. And at the forefront of this transformation is Senthilkumar Bose.
In the dynamic world of modern retail, data is the new currency, and customer experience is the ultimate differentiator. The challenge is no longer just collecting data, but connecting, understanding, and activating it at speed and scale. Leading the charge to solve this complex puzzle is Senthilkumar Bose.
The modern trading landscape is awash with unverified claims and social media hype. One trader is transforming this world with a distinctively different approach to the market. Agast Mishra is an index trader whose proven performance, backed by consistency, is changing the way traders view trust and accountability.
For SMEs, innovation often comes with a major hurdle: hiring specialized talent. Skilled professionals are expensive and scarce, but AI can help bridge the gap.
In this article, we'll take a closer look at the most popular OCR software used by finance and accounting teams in 2025. You'll learn how they differ, what features matter most, and which tool we recommend for teams looking to automate financial document processing at scale.
Engineers are at the forefront of this shift, collaborating across fields to address challenges like congestion, energy shortages, and environmental degradation. As Paul Wiedmaier notes, the integration of technology is enabling cities to operate more efficiently.
A group of authors has revealed how much Anthropic will pay them as part of the settlement for a piracy lawsuit.
How to avoid missing out on promising positions in an algorithm-driven world, where to find your place in the evolving tech landscape, and how to turn AI to your advantage—all of this is explained by Anna Gagarina, career development expert, founder of Job Mentor, an AI platform for career guidance.
Samantha, the AI robot, is designed to help students master AI applications and learn how to operate and control robots in an increasingly automated world, preparing them to be the real leaders of the future.
The ruling also sets a precedent for AI competition, requiring Google to share search data with rivals and potentially accelerating innovation across the sector.
Apple is facing a backlash for branding several perfectly good laptops, including the 2017 MacBook Pro and 2015 MacBook Air, as 'obsolete'.
From 'backed' to legally owned. Global Gold has created a transparent on-chain system that brings real bullion into a programmable and liquid economy.
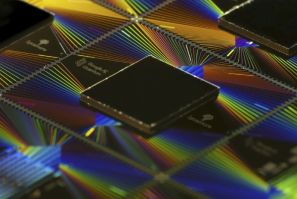
For all the fervor and hype surrounding artificial intelligence (AI), a problem constantly lurking in the shadows that rarely makes it into keynote speeches or glossy pitch decks—we're running out of compute. The problem needs to be taken seriously.
Founded in 2020, Do Big Studios has established itself as one of Roblox's most innovative forces. The studio not only develops chart-topping games but also invests in creators, helping them professionalize their work and scale their communities.
In the modern digital enterprise, data is the new currency, but its true value remains locked away without a master key. That key is strategic integration. Leading the charge in this critical domain is Shantan Kumar Bathini.
Legacy systems, data silos, and rigid architectures can cripple a company's ability to launch new services, personalize customer experiences, and streamline operations. At the forefront of dismantling these technological barriers is Shantan Kumar Bathini.
Over the past year, thousands of solo founders have launched products built almost entirely with generative tools. What used to take a team of engineers and designers can now be prototyped in days with AI-native platforms like Replit, Bolt, and Base44.