How To Avoid Ransomware: 8 Easy Tips
Speak to any IT professional, and it won't be long until you hear the word "ransomware." As the coronavirus outbreak has intensified, so too has cybercrime, including such infectious attacks on your computer as ransomware. But what is ransomware, exactly--and how can business owners protect their computers from it?
How Ransomware Works
Ransomware literally locks you out of your own data--including client data that you may be legally obligated to protect. Also known as ransom malware, it works via encryption (yes, that's a nerdy word but stick with me). In order for electronic information to remain private, much of the data that passes through the internet--including email--is encrypted. When you type, "Hi, how are you," the message would appear as random letters, numbers, and symbols to somebody unauthorized who tried to intercept it before it reached the person you sent it to. But the actual recipient has a "key" that allows them to unlock the message, unscrambling the gibberish into readable text.
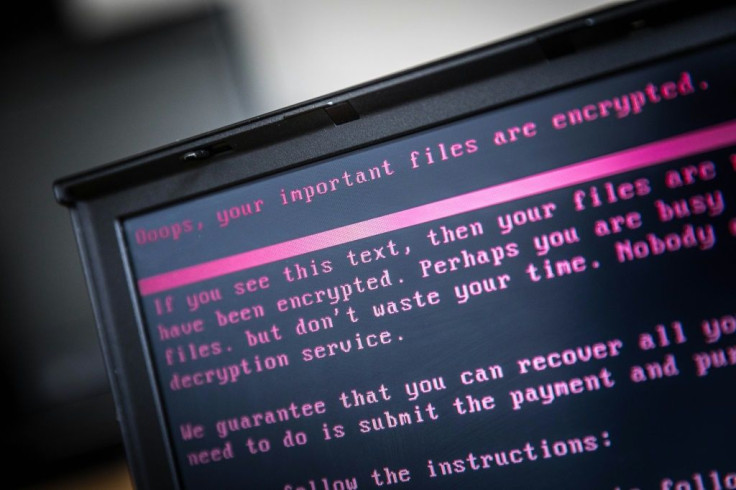
Usually, encryption works to protect you. But ransomware uses encryption for evil. A cybercriminal gains access to the data stored in your computer files and encrypts it--locks it up, so to speak. So, when you pull up any file or piece of information, it's unreadable and unusable. The only way to make it useable is with the encryption key--which you don't have.
This cyber-kidnapper then leaves you a message that demands some amount of money--usually, in the form of Bitcoin because it's hard to trace--in exchange for the key. (That's why it's called ransomware.) The attacker may also threaten to post the stolen data in a public place if you don't pay the ransom. But even if you pay, don't count on your computer magically return to its normal working state. Hackers put a lot more effort into writing the program that encrypts your data than they do the code to decrypt. So, sometimes the key simply doesn't work. That's why a ransomware attack can mean that your data is permanently lost.
More than nine out of 10 ransomware infections enter a company network through an infected e-mail that contains malware--a catch-all term that simply means a malicious piece of software. Think of it like a Trojan horse: Once it gets inside the walls of your cybercity, the malware gives the hackers access to the company network and operating system, where (in this case) they can start the evil encryption process.
Even worse, ransomware may sit in a computer for weeks or months, so it can infect your company's backup files too. Data stored offsite, like on a cloud-based server, is not as vulnerable; but it's definitely still susceptible, depending on how strong the server's firewall and other security protocols are.
What if You're Infected by Ransomware?
First, you should have a written disaster recovery plan in place, to be prepared for a ransomware attack. In fact, some compliance laws require a formal plan. The plan should include how an employee should report questionable computer behavior if they click on a link, who you will call if you're infected by ransomware, whether or not you will pay the ransom (the FBI says you should not) and how you will follow data breach disclosure laws that apply to you. You should also consider insurance to cover the costs associated with a data breach.
You will need a computer forensics firm, your IT company if you have one, a law enforcement contact, attorneys, and your insurance agent, only to name a few. Those people should be listed in your plan.
Notice that these are all things you should do now. If you do suffer an attack, there's not much you can do on your own to recover from a ransomware infection unless you have highly advanced IT knowledge.
How Can you Prevent Ransomware?
The best defense is a good offense, right? The easiest ways to lower your risk of being a ransomware victim starts with these measures, some of them just common sense.
- Keep all of your computers and network equipment up to date with security patches.
- Install anti-malware software on all computers.
- Use strong passwords. (Don't use ones that include your company name...duh!)
- Train employees not to click on attachments that don't come from a trusted source.
- Even if it comes from a trusted source, check the e-mail address of the sender and make sure it matches the address they've sent from in the past.
- Maintain a disconnected backup--that is, one that is not attached to your computer or its network--that is at least three months old. It should be safe to plug in and download data from it, as long as it's not attached to your infected computer too long.
- Talk to your IT company about installing a Unified Threat Management (UTM) device and limiting outbound traffic.
- Employees who are working remotely should only connect to your company network through a VPN.
It's estimated that, by 2021, a business will be attacked by ransomware every 11 seconds.
And don't think that ransomware only targets large corporations or organizations. Any size company is vulnerable, especially now that its workers might be accessing data offsite, on their personal computers via the internet.
A large part of preventing ransomware is setting up or upgrading your computer system securely, or beefing up its security. If you have to call in an IT professional to do so, consider the expense an investment. It'll certainly be more reasonable than paying a hijacker's ransom.
Tim Parker is co-founder and President of The Web Group, an IT consulting firm based in Florida.
© Copyright IBTimes 2025. All rights reserved.





















